Cybersecurity
TARA in Automotive Cybersecurity: A Complete Guide to Threat Analysis and Risk Assessment
Threat Analysis and Risk Assessment — TARA — is the analytical foundation of automotive cybersecurity. Required by ISO SAE 21434, referenced in UN R155/WP.29, and codified in the SAE J3061 guidebook, TARA is the process through which automotive organizations identify what can go wrong with a vehicle’s cybersecurity, how severe the consequences would be, and what needs to be done about it.
Yet TARA is also one of the most consistently underestimated activities in automotive development programs. Organizations that treat it as a documentation exercise — rather than a rigorous analytical process — produce compliance artifacts that fail to accurately characterize their threat landscape, leading to inadequate cybersecurity requirements, missed vulnerabilities, and regulatory exposure.
What Is TARA in the Context of ISO SAE 21434?
In ISO SAE 21434, TARA is formally defined in Clause 15 (Threat Analysis and Risk Assessment) and is required at the item level — meaning for every vehicle system or component that is within the cybersecurity scope of the development program. The TARA process produces three primary outputs: a list of threat scenarios (with associated damage scenarios), a risk assessment for each scenario, and cybersecurity goals that define acceptable risk levels.
These cybersecurity goals then drive the entire downstream engineering process: requirements, design constraints, implementation guidance, and test cases. A TARA that misses a significant threat scenario creates a blind spot that propagates through every subsequent engineering activity.
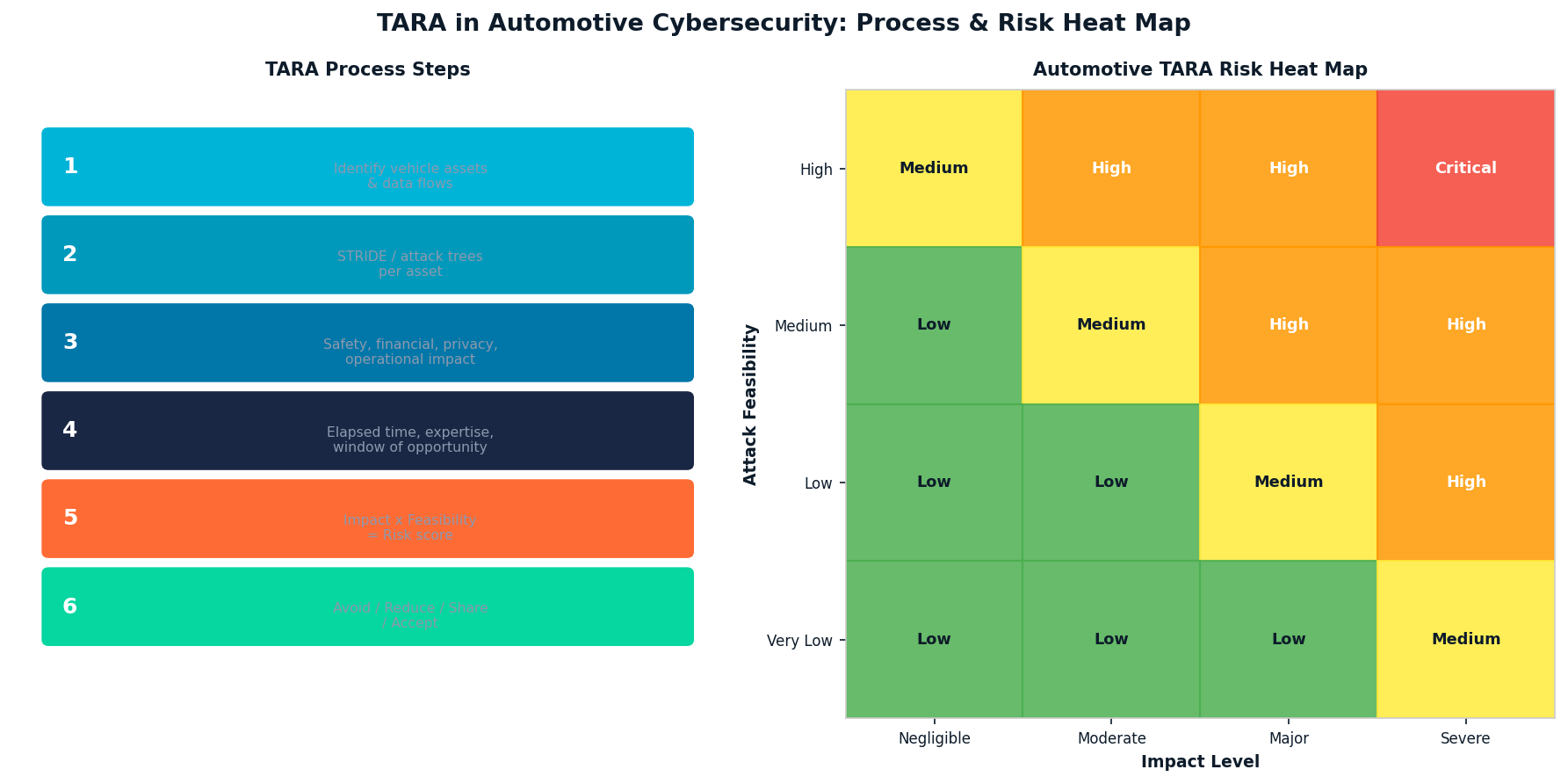
The Six Steps of Automotive TARA
| Step | Activity | Key Output |
| 1. Asset Identification | Identify vehicle assets, data, and functions | Asset register with cybersecurity relevance |
| 2. Threat Modeling | Enumerate threats per asset using STRIDE/attack trees | Threat scenario catalog |
| 3. Impact Assessment | Evaluate Safety, Financial, Operational, Privacy impact | Impact rating per scenario (1-4 scale) |
| 4. Attack Feasibility | Assess elapsed time, expertise, equipment, knowledge | Feasibility rating per threat |
| 5. Risk Determination | Combine impact and feasibility → risk value | Risk matrix with prioritization |
| 6. Risk Treatment | Define treatment: Avoid / Reduce / Share / Accept | Cybersecurity goals and treatment decisions |
STRIDE and Attack Trees: Core Threat Modeling Methods
ISO SAE 21434 does not mandate a specific threat modeling methodology, but STRIDE (Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, Elevation of Privilege) and attack trees are the most widely used approaches in automotive TARA practice. STRIDE provides a systematic taxonomy that ensures analysts consider all relevant threat categories across each asset. Attack trees enable complex multi-step attack sequences to be documented and analyzed, which is important for ECU-level threats where an attacker must chain multiple exploits to achieve their goal.
Impact Categories in Automotive TARA
| Impact Category | Examples | Severity Scale |
| Safety (S) | Physical harm to occupants, road users | S0 (no harm) to S3 (life-threatening) |
| Financial (F) | Warranty costs, recalls, liability | F0 to F3 (based on monetary threshold) |
| Operational (O) | Vehicle unavailability, function loss | O0 to O3 (based on scope of disruption) |
| Privacy (P) | Personal data exposure, tracking | P0 to P3 (per GDPR severity categories) |
TARA Automation: Why Manual Processes Fail at Scale
Modern vehicles contain 100+ ECUs communicating across multiple network domains. A single vehicle program may require TARA analyses for dozens of items and components, each with hundreds of potential threat scenarios. Performing this work manually in spreadsheets creates consistency problems, traceability gaps, and significant rework burden when designs change.
Automated TARA tools that maintain structured asset-threat-risk linkages, propagate design changes to affected analyses, and generate auditable compliance evidence reduce both cycle time and error rate by an order of magnitude compared to manual methods.
PlaxidityX’s Security AutoDesigner is purpose-built for automotive TARA automation, with structured support for ISO SAE 21434 Clause 15 processes, attack tree construction, and automatic traceability from threat scenarios to cybersecurity requirements. For a blog-level introduction to TARA in risk management, PlaxidityX’s guide to automating automotive cybersecurity risk management provides practical context.
TARA in the Supply Chain: Sharing and Integrating Analysis
A persistent challenge in automotive TARA is that OEMs and suppliers each perform analyses that must ultimately be consistent with each other. When an OEM’s TARA identifies a threat to a supplier-provided ECU, the supplier’s own TARA must either address that threat or explicitly accept the residual risk at the organizational interface. ISO SAE 21434 Clause 5 (Distributed Development) defines the contractual and technical obligations that govern this handoff.
Further Reading
The SAE J3061 cybersecurity guidebook provides the foundational threat modeling guidance that ISO SAE 21434 builds upon. For independent coverage of TARA methodology developments, AllTechNews on automotive cybersecurity analysis tracks industry practice and tooling.
Conclusion
TARA is not a one-time compliance activity — it is a living analytical process that must be maintained as vehicle designs evolve, new vulnerabilities are discovered, and threat landscapes shift. Organizations that invest in structured, automated TARA processes produce better security requirements, pass regulatory audits more efficiently, and build a genuine organizational memory of their cybersecurity risk posture across programs and generations of vehicles.
Cybersecurity
Copilot Studio Security: How Kanopy Governs the Shadow AI Agents Hiding in Plain Sight
At a Glance
- Microsoft Copilot Studio has made it possible for any business team to build and deploy AI agents in days – without involving IT or security. The result is a rapidly growing population of shadow AI agents operating inside enterprise environments with real permissions, real data access, and zero security oversight.
- Copilot Studio security is not a feature gap that Microsoft will close with a settings toggle. It is a governance problem that emerges from the platform’s fundamental design: business users can build, publish, and connect agents to sensitive data without a single security review.
- Kanopy Security provides the continuous discovery, risk assessment, and governance layer that transforms Copilot Studio’s business-built agents from an ungoverned liability into a managed, secured asset class.
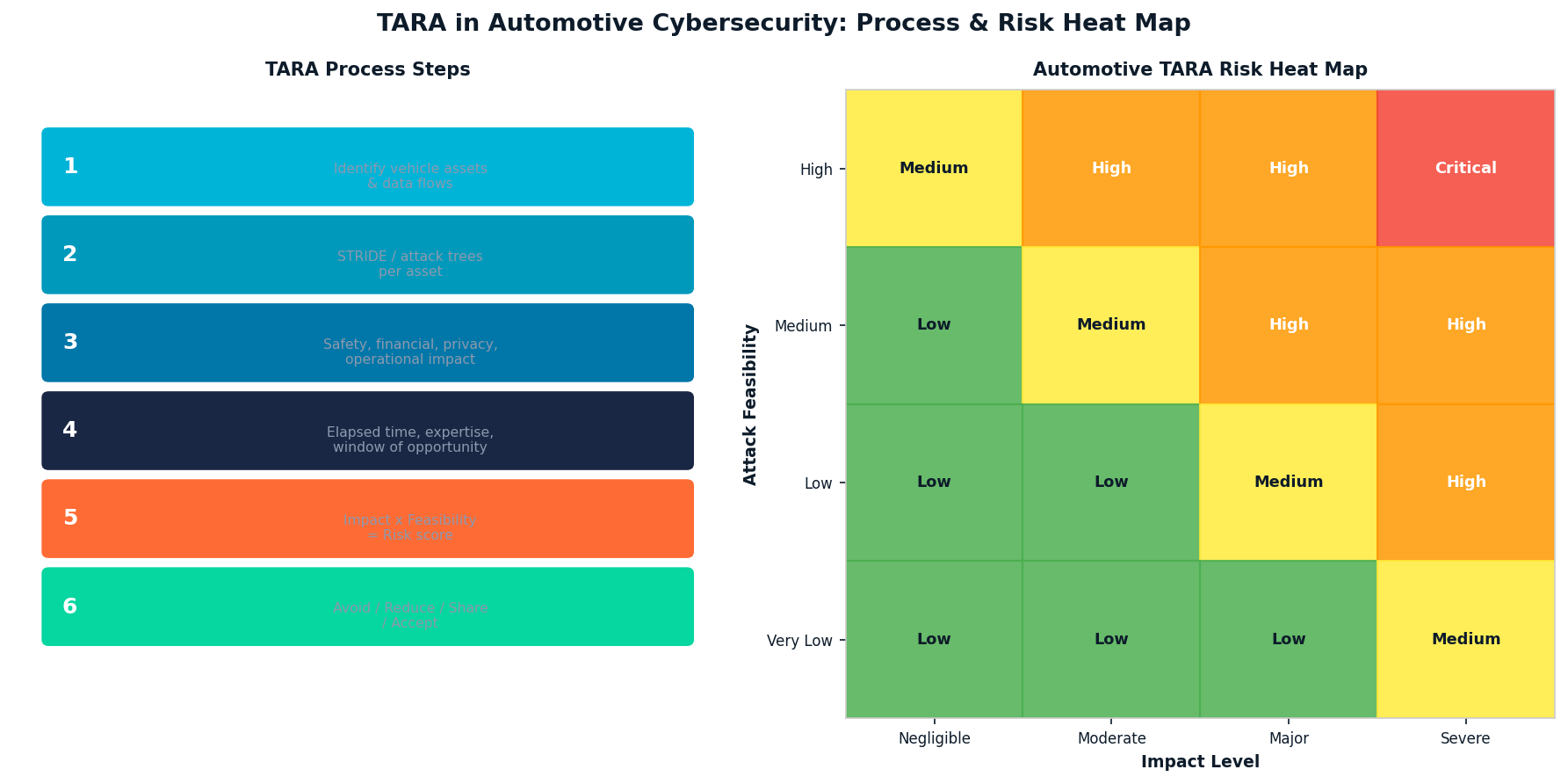
The pace at which Microsoft Copilot Studio agents are being created inside enterprise environments has outrun every reasonable security team’s capacity to keep up. A customer service team builds an agent connected to Dynamics 365. A finance team deploys an agent with access to SharePoint and Power BI. An HR team publishes an agent that can query sensitive employee data. None of these agents went through a security review. None of them were inventoried. And in most organisations, nobody in the security team even knows they exist. That is the copilot studio security problem — and it is growing faster than any manual governance process can address.
Why Copilot Studio Creates a Shadow AI Security Problem
Shadow AI security has typically referred to employees using unsanctioned public AI tools – ChatGPT, Claude, Gemini – without organisational oversight. Copilot Studio creates a more complex variant of the same problem: shadow AI that operates with enterprise identities, enterprise permissions, and enterprise data, built by people who had no security training when they built it.
Business teams building Copilot Studio agents face no mandatory security checkpoint. The platform’s citizen developer model – which is genuinely powerful for productivity – does not include a security review gate before an agent is published and begins operating. Agents are frequently granted broad permissions to avoid breaking workflows. Once deployed, they can act automatically, pulling data from SharePoint, OneDrive, Dataverse, or connected SaaS applications and surfacing or transmitting it in ways that were never reviewed for data governance compliance.
Orphaned agents compound the problem. When the team member who built an agent leaves or moves to a different role, the agent continues operating – often with the original creator’s access credentials or a service principal that was never reviewed for appropriate scope. Kanopy’s research across enterprise Microsoft 365 environments consistently finds that a significant proportion of Copilot Studio agents are orphaned, overprivileged, or connected to data sources that their owners did not intend to expose.
What Kanopy Provides for Copilot Studio Security
Kanopy’s Copilot Studio security capability begins with discovery – and in most organisations, the discovery results alone are significant. Kanopy builds a living inventory of every Copilot Studio agent in the environment: who built it, when it was last active, what data connections it has, what permissions it operates with, and whether it has been published externally. Many security teams, upon seeing this inventory for the first time, discover agents they did not know existed and data connections they would not have approved.
From inventory, Kanopy moves to continuous risk assessment. Each agent is evaluated against a defined risk profile: overprivileged access, connections to sensitive data categories, absence of appropriate authentication controls, orphaned ownership, and published channels that expose the agent beyond its intended scope. Risk findings are surfaced with the context that makes them actionable – not just a vulnerability score but an explanation of what the risk means and what remediation looks like.
Remediation in Kanopy is designed for the operational reality of enterprise environments: one-click remediation for common issues that routes fixes to the appropriate business user, and detailed guidance for security team action on higher-complexity findings. The goal is not to give security teams more alerts to manage – it is to close the gap between identifying a risk in a Copilot Studio agent and actually reducing it. Explore Kanopy’s full Copilot Studio security capability at the Kanopy Copilot Studio Security page, and discover how shadow AI security across the full enterprise AI estate is addressed at kanopysecurity.com.
Frequently Asked Questions
Q1: What makes Copilot Studio security different from securing other enterprise applications?
A: Copilot Studio agents are built by business users without security training, operate autonomously with enterprise permissions, and can act on data in real time. Unlike traditional applications, they have no mandatory security gate before deployment, can be created and modified rapidly, and may accumulate permissions over time without review. This makes continuous, automated governance essential rather than periodic manual review.
Q2: Why is shadow AI security a concern specifically for Copilot Studio environments?
A: Copilot Studio enables business teams to create and deploy AI agents without IT or security involvement. These agents operate with real enterprise credentials and access real data – but because they are built outside formal software development processes, they typically receive no security review. This creates shadow AI: autonomous systems operating inside the enterprise with unknown risk profiles.
Q3: Does Microsoft’s native Copilot Studio governance cover the security risks Kanopy addresses?
A: Microsoft’s native controls – Power Platform Admin Center, Purview DLP, data policies – provide important baseline governance but are not designed to continuously discover every agent, assess risk at the agent level, track orphaned agents, or provide the actionable remediation workflow that enterprise security teams need. Kanopy operates as a dedicated security layer on top of Microsoft’s native controls.
Q4: How does Kanopy discover Copilot Studio agents that weren’t formally registered or inventoried?
A: Kanopy connects directly to the Microsoft 365 and Power Platform ecosystem, automatically discovering every Copilot Studio agent regardless of whether it was formally inventoried. The discovery process surfaces agents that security teams did not know existed, maps their data connections and permissions, and identifies orphaned agents that have lost active ownership.
Q5: Can Kanopy remediate Copilot Studio security issues automatically?
A: Kanopy provides one-click remediation for common security issues — over-broad permissions, missing authentication controls, exposed publishing channels – that routes appropriate fixes to business users or security teams depending on the complexity of the issue. For higher-severity findings, Kanopy provides detailed remediation guidance that security teams can action directly.
Cybersecurity
Microsoft Power Platform Security: The Risks CISOs Cannot Afford to Ignore
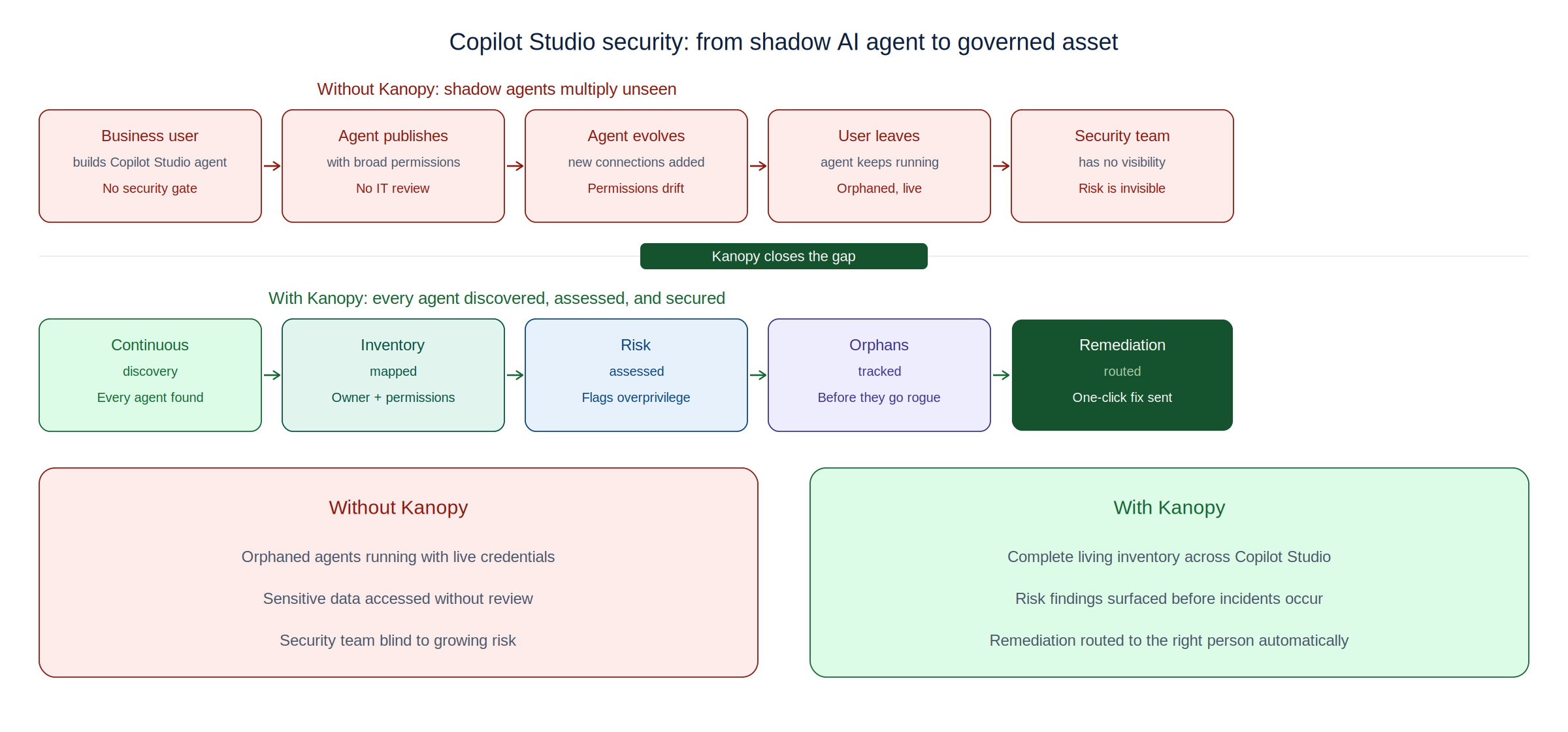
Microsoft Power Platform is now one of the most widely deployed technology ecosystems in the enterprise. Power Apps, Power Automate, Power BI, and Copilot Studio collectively enable millions of business users to build custom applications, automate complex workflows, analyze sensitive data, and deploy AI agents — all without writing a single line of code. The productivity gains are real and significant. The security implications are equally real — and far less often discussed.
Unlike traditional enterprise applications that pass through formal development and security review processes, Power Platform apps and automations are typically built by business users working at high speed, with limited security training and no mandatory AppSec review. The result is an ecosystem that grows faster than any security team can track, and faster than Microsoft’s native governance tools are designed to manage. This is the core challenge that purpose-built platforms for microsoft power platform security are designed to address.
Understanding the Power Platform Ecosystem
Power Platform is not a single product — it is an integrated ecosystem of tools that share a common data layer, a common connector framework, and a common identity model based on Microsoft Entra. Understanding each component’s security implications is essential for organizations seeking to govern the platform effectively:
| Component | Primary Function | Key Security Concerns |
| Power Apps | Custom business application development | External data exposure, excess permissions |
| Power Automate | Workflow and process automation | Automated data exfiltration, unvetted triggers |
| Power BI | Business intelligence and data analytics | Sensitive data in reports, oversharing dashboards |
| Copilot Studio | No-code AI agent creation | Prompt injection, shadow agents, data leakage |
| Dataverse | Shared enterprise data platform | Misconfigured access, cross-app data exposure |
The shared architecture is both the platform’s strength and a key source of security risk. Because all components operate within the same data and identity model, a misconfiguration or vulnerability in one component can cascade across the others. An overly permissive Power Automate flow, for example, can move data from Dataverse into an external system in ways that affect every app that depends on that data.
The Scale of Enterprise Power Platform Deployments
One of the most underappreciated aspects of Power Platform security is the sheer scale of typical enterprise deployments. Organizations that believe they have dozens of Power Platform apps typically have thousands. According to data from Nokod Security, the average large enterprise environment contains more than 10,000 Power Platform apps and automations — far exceeding what any team could review manually.
The scale problem is compounded by the platform’s accessibility. Because power platform security governance requires visibility across all of these assets simultaneously, manual approaches are operationally impossible at enterprise scale. Automation is not an option — it is a necessity.
Top Power Platform Security Risks
Based on real-world enterprise security assessments, the following risk patterns consistently emerge across Power Platform deployments:
- Data Leakage via Connectors: Power Automate and Power Apps connect to hundreds of third-party services via the Microsoft connector framework. Without proper Data Loss Prevention policies, sensitive data can flow to unauthorized destinations automatically, often without the app builder’s awareness.
- Excessive Sharing: Power Apps can be shared with individual users, security groups, or the entire organization. Apps shared tenant-wide expose their underlying data connections to all employees — a common misconfiguration that security teams rarely catch without automated scanning.
- Power BI Data Security: Power BI reports and dashboards often contain sensitive financial, operational, or customer data. Without row-level security and workspace governance, this data can be exposed to audiences far beyond what the report creator intended.
- Shadow Engineering: Business units build Power Platform solutions outside of IT visibility, creating a growing inventory of unmonitored apps that may expose sensitive data, violate compliance requirements, or become orphaned when their creators change roles.
- Injection Vulnerabilities: Power Apps connected to SQL databases or other data sources are vulnerable to injection attacks, particularly when input validation is handled by the app builder rather than by a trained developer.
- Supply Chain Risk: Connectors and custom APIs embedded in Power Platform solutions introduce third-party dependencies that carry their own security risks, including compromised endpoints and unauthorized data access.
Gartner has predicted that low-code/no-code development will account for more than 70% of new enterprise application activity. As Power Platform adoption accelerates, these risks will grow proportionally unless organizations implement systematic governance.
Power BI Security: A Frequently Overlooked Attack Surface
Power BI occupies a unique position in the Power Platform security landscape. Unlike Power Apps and Power Automate, which are primarily operational tools, Power BI is designed specifically for distributing data broadly across the organization. Reports and dashboards are regularly shared with large internal audiences and, in many cases, embedded in external-facing portals.
This broad distribution model creates significant Power BI data security risks. Reports may contain embedded credentials or sensitive query logic. Workspaces may be shared without appropriate access controls. Data refresh schedules may pull from production systems without proper service account governance. And premium capacity environments may lack the monitoring required to detect unusual data access patterns.
Managing these risks requires the same combination of inventory, policy enforcement, and automated monitoring that governs the broader Power Platform. For organizations seeking to address data leakage prevention across their entire Power Platform environment, a unified approach that covers all components — including Power BI — is essential.
How Nokod Addresses Power Platform Security
Nokod Security was built specifically for the low-code/no-code security challenge. Its platform connects to Power Platform environments and, within minutes, delivers a complete inventory of every app, flow, agent, and data connection — including assets that IT has never seen. From that inventory, Nokod automatically surfaces the risks that matter: excessive permissions, unauthorized sharing, connector policy violations, injection vulnerabilities, and data exposure paths.
For Power BI specifically, Nokod scans workspace configurations, sharing settings, and data access patterns to identify dashboards and reports that expose sensitive data to unintended audiences. One-click remediation options allow security teams to address identified issues at scale without requiring app-by-app manual review.
Fortune 500 companies across insurance, healthcare, and financial services have deployed Nokod to bring security rigor to their Power Platform environments. The typical finding: the actual number of apps and automations is between five and ten times larger than what IT believed existed — and a significant proportion carry high-severity security findings that require immediate remediation.
For a detailed analysis of Power Platform security risks and remediation strategies, see this comprehensive guide at techpr.online.
For background on the broader low-code security landscape, the Wikipedia article on Low-code development platform provides useful context.
Conclusion
Microsoft Power Platform has become indispensable to enterprise operations — and one of its most significant security blind spots. The combination of rapid citizen development, complex multi-component architecture, and organizational scale creates risks that manual governance processes cannot address. Nokod Security provides the automated visibility, risk detection, and remediation capabilities that Power Platform environments require — enabling organizations to accelerate digital transformation on Power Platform with confidence that the security team has the oversight the enterprise demands.
Cybersecurity
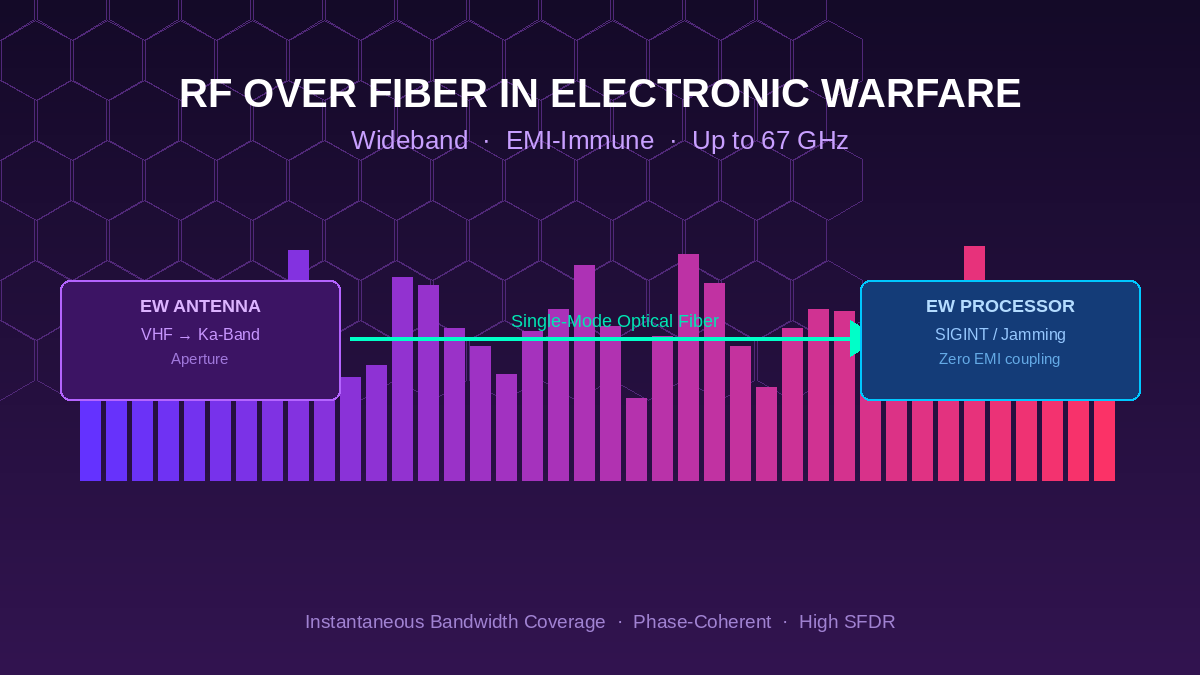
RF over Fiber in Electronic Warfare: How Optical Links Solve the EW Signal Distribution Challenge
Introduction
Electronic warfare systems operate at the intersection of high frequency, wide bandwidth, and hostile electromagnetic environments. The signals of interest span from VHF tactical communications bands through X-band and Ka-band radar frequencies, often demanding instantaneous coverage across tens of gigahertz. Connecting antennas, sensors, and processing hardware across the physical distances of a ship, aircraft, or ground vehicle while preserving signal fidelity at these frequencies has historically been one of the most demanding challenges in platform integration. RF over fiber technology for EW and radar applications has emerged as the definitive solution for this distribution problem.
Why Coaxial Cables Fail in Modern EW Environments
Coaxial cable has served as the backbone of RF signal distribution for decades. However, its limitations become severe when pushed to the demands of modern electronic warfare architectures. At frequencies above 6 GHz, high-grade coaxial cable loses approximately 100 dB or more per 100 meters, making long antenna-to-receiver runs impractical without multiple inline amplifiers. Each amplifier adds noise, non-linearity, and a potential point of failure.
Beyond attenuation, coaxial systems are intrinsically susceptible to electromagnetic interference. In an EW environment, the platform itself may be the source of powerful jamming signals, radar emissions, or electronic attack pulses. These signals couple into long coaxial runs, degrading the sensitivity and dynamic range of receive chains. Heavy copper shielding adds weight, and ground loops between equipment racks create noise floors that can obscure low-level signals of interest.
The Optical Advantage for Wideband Signal Distribution
RF over fiber (RFoF) links convert the RF signal to an optical carrier at the source (typically at the antenna aperture), transmit the modulated light through a single-mode optical fiber, and convert it back to RF at the processing point. The optical fiber itself is immune to electromagnetic interference, introduces no ground loops, weighs a fraction of comparable coaxial solutions, and supports bandwidths from DC through millimeter-wave frequencies across a single physical medium.
The frequency coverage advantage is particularly significant for EW applications. While conventional RFoF suppliers typically support frequencies to 6 GHz, high-frequency RF over fiber systems designed for EW and radar cover frequencies from below 1 GHz up to 67 GHz and beyond. This enables a single fiber link to simultaneously carry L-band GPS, S-band communications, C-band fire control radar, X-band surveillance radar, and Ka-band sensor signals, dramatically reducing the fiber count and connector complexity of multi-band EW suites.
Key Performance Parameters for EW RFoF Links
Electronic warfare applications impose specific performance requirements that go beyond what is adequate for commercial telecommunications use cases. The following parameters are particularly critical:
- Spurious-Free Dynamic Range (SFDR): EW systems must detect low-level signals in the presence of powerful nearby emitters. A high SFDR allows the analog fiber link to preserve the full dynamic range available at the antenna aperture, deferring digitization to the processing subsystem where dedicated ADC architectures can handle the burden.
- Noise Figure: The RFoF link adds noise to the received signal chain. In receive-only applications, a low-noise figure preamplifier at the antenna end can recover most of this penalty and keep the system noise figure consistent with coaxial alternatives.
- Phase Coherence: Coherent radar and electronic intelligence (ELINT) systems require multiple antenna channels to maintain precise phase relationships. Phase-matched RFoF link pairs ensure that angle-of-arrival measurements and coherent beamforming calculations remain accurate.
- Instantaneous Bandwidth: EW receivers are often required to process signals anywhere across a multi-gigahertz tuning range without prior knowledge of the signal’s frequency. A wideband fiber link that supports the full instantaneous bandwidth of the receiver avoids the need for preselector filtering that could block signals of interest.
Platform Integration: Ship, Aircraft, and Ground Vehicle Applications
The physical integration benefits of optical fiber are especially pronounced on military platforms where space and weight are at a premium. A single optical fiber with an outer diameter of 2-3 mm can replace a bundle of coaxial cables that might weigh several kilograms per meter. On large surface combatants with antenna apertures located at mast height, this translates to hundreds of kilograms of weight reduction per fiber run replaced.
On aircraft and unmanned aerial vehicles, the weight savings directly translate to increased payload, endurance, or fuel efficiency. The flexibility of optical fiber also simplifies routing through tight conduit paths and around structural members where rigid coaxial assemblies would require complex custom fabrication. Fiber runs can be field-terminated and replaced far more quickly than precision coaxial assemblies, supporting faster maintenance turnaround times.
Optical Delay Lines in EW Signal Processing
Beyond signal distribution, optical delay lines play a direct role in EW signal processing architectures. Photonic time-stretch analog-to-digital converters use chirped fiber delay elements to effectively slow down high-bandwidth RF signals before digitization. Radar warning receivers and jamming systems use precise delay lines to generate coherent responses to intercepted signals. Optical delay line solutions for EW applications provide the stable, phase-matched delays that these advanced processing architectures require, with frequency coverage that extends through Ka-band and V-band signals beyond the reach of conventional delay line technology.
Conclusion
Electronic warfare is one of the most demanding applications in the RF domain, and signal distribution quality directly determines how well a system can detect, classify, and counter threats. RF over fiber technology addresses the fundamental limitations of coaxial distribution by offering immunity to interference, dramatic weight savings, and frequency coverage that extends to millimeter-wave bands. As EW systems continue to expand their frequency coverage and require tighter integration of multiple sensor apertures, optical signal distribution will become increasingly essential to achieving the performance goals that modern defense platforms demand.
For further context on the evolving frequency landscape in defense electronics, Microwave Journal provides authoritative coverage of EW system developments and RF photonics technology.
-

 Business Solutions2 years ago
Business Solutions2 years agoLive Video Broadcasting with Bonded Transmission Technology
-

 Business Solutions1 year ago
Business Solutions1 year agoThe Future of Healthcare SMS and RCS Messaging
-

 Business Solutions2 years ago
Business Solutions2 years ago2-Way Texting Solutions from Company Message Services
-

 Business Solutions2 years ago
Business Solutions2 years agoCommunication with Analog to Fiber Converters & RF Link Budgets
-

 DSRC Communication1 year ago
DSRC Communication1 year agoThe Crossroads of Connectivity: DSRC vs. C-V2X Technologies in Automotive Communication
-
Electronics3 years ago
AI Modules and Smart Home Chips: Future of Home Automation
-

 Business Solutions2 years ago
Business Solutions2 years agoWholesale SMS Platforms with OTP Services
-
 Business Solutions2 years ago
Business Solutions2 years agoAerial Wind Turbine Inspection with Advanced Camera Drones




