Cybersecurity
Industrial Cybersecurity Companies
Industrial Cyber Security: More than just one company
The technological landscape is changing extensively with the advent of integrated systems with accessibility driving this development. Manufacturing and plant operation machines that used to have an air-gap between themselves and other systems are now dwindling with the push for integration. This is not necessarily a bad thing as it aids productivity and profitability. Linking systems is not just reserved for the company itself but also its supply chain pulling in materials and components as they are need. In fact, in the recent Covid-19 pandemic the need to switch suppliers quickly has allowed supermarkets and other essential industries to remain open.
Unfortunately, this advancement has increased challenges when it comes to cybersecurity. Hackers in recent years have attacked power stations, factories, hospitals and infrastructure. Some for profit and others working within governments to disrupt another competing countries GDP.
Some attack vectors have involved the exploitation of software supplied by 3rd contractors. For example, a large platform such as a product management lifecycle (PLM) software that is utilised extensively in manufacturing sectors to digitally replicate the design and manufacturing processes inevitably use existing software that it integrates in a modular basis. If any one of dependent software has malicious content it is unlikely that it will be detected at the time of installation and roll out.
Hackers recently used this process to gain access to a worldwide company all through gaining access through a smaller company and creating a backdoor that allowed them to then exploit the companies supply chain and sell industrial secretes to competitors. While this was not PLM software that was involved it was similar in scale and integration. Interestingly the hackers waited for years until the 3rd party software was widespread in other companies from other installations. This was a huge scandal as it took a long time for the software that they added was flagged, and through a long investigation the extent of the issue realised.
Industrial cybersecurity companies
Industrial cybersecurity companies hire the best and brightest for their teams, they work every day on cybersecurity activities and upskilling on the latest threats. Sometimes you just need specialists that specialise in cyber security. The challenge is still keeping up with new approaches.
Currently operational technology (OT) also called industrial control systems (ICS) are being targeted by hackers due to the extensive information about this technology readily available on the internet. This can be in the form of maintenance documentation, a method used to hack wireless printers recently and gaining network access from there. User instructional documentation or installation procedures may be used in a similar light. Some hackers use online videos for similar information. While one source may cover one item of interest to hackers another may complete the puzzle of how to gain access to a system.
Shodan: no coding, login or hacking experience necessary
One of the best examples of finding an exploitable route is the website Shodan. This is well known in the hacking community and is one of the best sites to see poorly maintained cybersecurity. A lot of white hat hackers use the site to find servers that are accessible and then contact the company to tell them that they need to fix the issue. Some companies listen while others ignore this advice. The site allows anyone to access these servers without a login required and free for a handful of searches. You could search your industry and click a remote connection to gain access to a system that may not even be password protected. This site shows a ‘grey area’ in hacking because a server that does not have a password for an accessible port is potentially legal to gain access to. Shodan allows anyone to find and access these sites which include power stations and airports with no restriction and with no coding or hacking experience needed.
Why can this occur; simply put due to contractors providing a platform and documenting that a client must harden their server that it has been used. The client however may not know anything about computers and leave ports such as FTP and remote access ports open and not providing a system password as they may forget what it is or have other users that use it. These are not old challenges, check out if your company is on Shodan and use Industrial cybersecurity companies peace of mind.
Cybersecurity
What Is Shadow AI? A Complete Guide for Enterprise Security Teams
Artificial intelligence has moved faster than any technology governance program in history. While organizations debate AI adoption policies, employees have already decided — they are using AI tools today, with or without approval. This phenomenon is known as shadow AI, and it has become one of the most pressing security challenges facing enterprise security leaders in 2025 and beyond.
This guide explains what shadow AI is, why it happens, what risks it introduces, and how organizations can gain visibility and control without blocking the productivity benefits that AI delivers.
What Is Shadow AI?
Shadow AI is the use of artificial intelligence tools, applications, and services by employees without the knowledge, approval, or governance of the organization’s IT or security teams. It ranges from an individual pasting proprietary source code into ChatGPT, to entire departments deploying unapproved AI plugins that access sensitive customer data, to developers using AI coding assistants that capture intellectual property as training data.
The term builds on the older concept of shadow IT — the use of unauthorized software and cloud services — but shadow AI carries a fundamentally higher risk profile. Unlike a rogue SaaS subscription, AI tools actively process, analyze, and in some cases retain enterprise data. The information shared does not simply sit in an unauthorized system; it may train public models, be accessible to third parties, or persist in ways the organization cannot audit or retract.
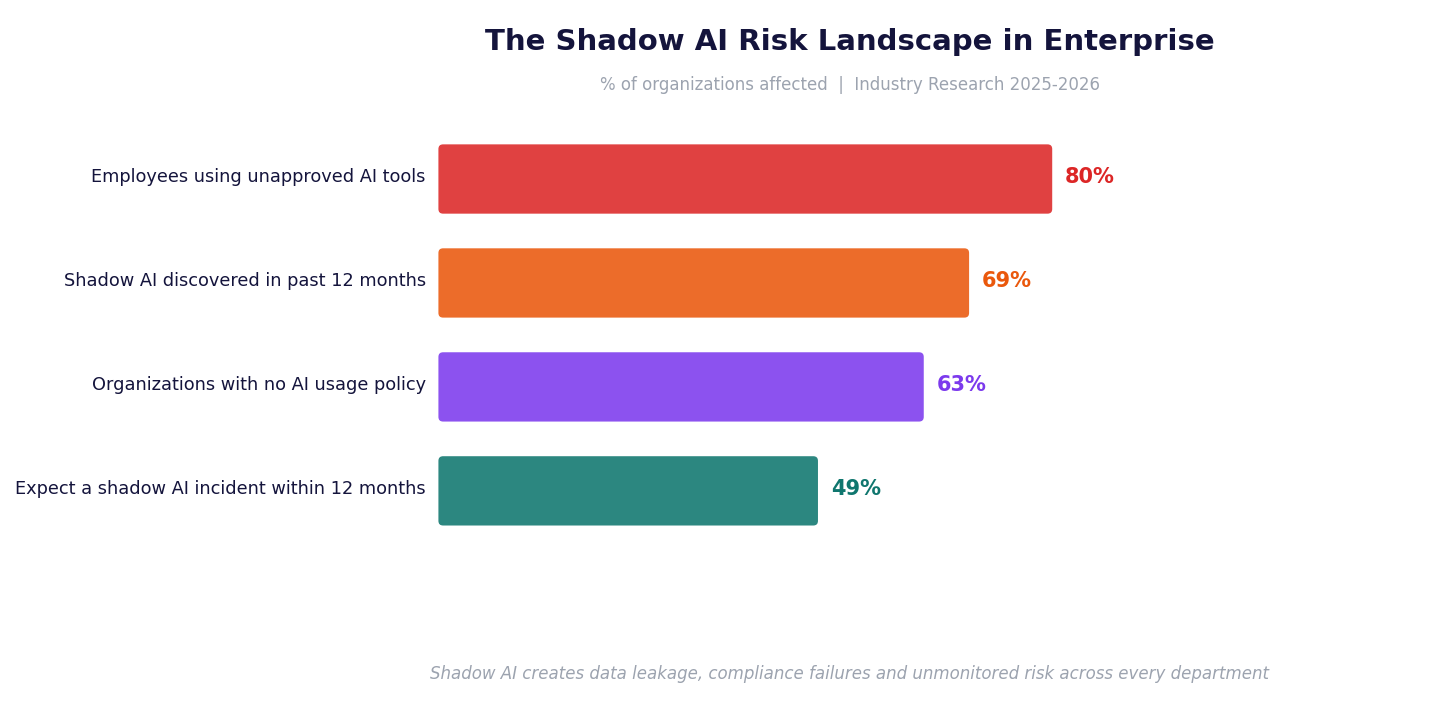
According to research from industry analysts, more than 80% of employees now use unapproved AI tools in their work. Platforms like
Ovalix offer organizations a dedicated shadow AI detection engine that identifies every AI tool in use across the organization — including tools employees have never disclosed.
Why Does Shadow AI Happen?
Shadow AI is not the result of malicious intent. It is almost always a productivity story. Employees encounter an AI tool that dramatically accelerates their work, and they begin using it before — or instead of — waiting for an approval process that may take weeks or months. Three factors consistently drive shadow AI adoption:
- Approval bottlenecks: AI tools emerge faster than procurement cycles. By the time IT evaluates one tool, five new alternatives have launched.
- Performance pressure: Employees feel competitive pressure to deliver faster results and AI tools offer an immediate advantage.
- Policy gaps: As of 2025, more than one-third of organizations have no AI acceptable use policy in place, leaving employees to make their own judgments about what is safe.
The problem is compounded by the fact that most AI tools are browser-based and require no installation, making them invisible to conventional endpoint security tools and network monitoring solutions that were never designed to detect them.
The Security Risks of Shadow AI
Shadow AI creates risk at every layer of the enterprise security stack. The most significant risk categories include:
Data Leakage
The most immediate and measurable risk is data exposure. Employees routinely share sensitive information with public AI tools: customer records, financial forecasts, legal contracts, source code, and personally identifiable information (PII) or protected health information (PHI). In a widely cited incident, engineers at a major semiconductor company pasted proprietary code and internal meeting notes into ChatGPT, creating a data breach that could not be reversed.
Once data is submitted to a public AI model, the organization loses control of it. Depending on the platform’s terms of service, that data may be used to train future versions of the model, accessible to the service provider, or retained indefinitely.
Compliance Failures
Regulations including the EU AI Act, GDPR, HIPAA, and various financial services frameworks impose strict requirements on how organizations handle and process personal data. When employees share regulated data with unauthorized AI tools, the organization may be in violation without its compliance team ever knowing.
This is particularly dangerous in healthcare, where patient data shared with an unapproved AI application may constitute a reportable HIPAA breach. In finance, sharing non-public information with external systems can trigger securities compliance concerns.
Account and Licensing Risk
A specific and often overlooked dimension of shadow AI is the use of personal accounts to access AI platforms. When an employee uses a free personal ChatGPT or Claude account for work, the data they share is governed by consumer terms of service, not enterprise data processing agreements. The organization has no visibility, no audit trail, and no contractual protection.
The Ovalix AI security platform addresses this specifically, with the ability to detect whether employees are using personal accounts versus approved enterprise accounts and enforce policy in real time.
How to Detect and Control Shadow AI
Effective shadow AI management follows a four-stage process:
| Stage | What It Involves | Why It Matters |
| Discover | Identify every AI tool in use across the organization, including browser extensions and personal accounts | You cannot govern what you cannot see |
| Monitor | Track how employees interact with AI tools in real time, including what data they share | Continuous visibility surfaces risks as they happen |
| Govern | Establish and enforce an AI acceptable use policy aligned to regulatory requirements | Policy without enforcement is ineffective |
| Educate | Guide employees toward approved AI tools with real-time feedback, rather than simply blocking access | Blocking drives AI underground; guidance changes behavior |
The key shift organizations must make is from reactive blocking to proactive governance. Banning AI tools consistently fails because employees find workarounds. The organizations that successfully manage shadow AI are those that build a governed AI environment where approved tools are accessible, policies are enforced automatically, and employees receive guidance in the moment rather than after an incident.
The Business Case for Addressing Shadow AI Now
According to IBM’s Cost of a Data Breach report, shadow AI incidents add an average of $670,000 to the cost of a data breach. Gartner predicts that by 2030, more than 40% of enterprises will experience a security or compliance incident directly linked to unauthorized AI use. The financial and reputational stakes are no longer theoretical.
The good news is that shadow AI is a solvable problem. Organizations that invest in AI visibility and governance infrastructure now will be significantly better positioned to scale AI adoption safely — accelerating innovation rather than blocking it.
For a deeper look at how leading organizations are approaching this challenge, the
OWASP LLM Top 10 provides a widely referenced framework for understanding AI security risks across the enterprise.
Conclusion
Shadow AI is not a future problem. It is already present in virtually every organization that employs knowledge workers. The employees using unapproved AI tools are not acting carelessly — they are using the most effective tools available to them. The security leader’s task is not to stop them, but to make the safe path the easy path: visible, governed, and compliant by design.
Cybersecurity
TARA in Automotive Cybersecurity: A Complete Guide to Threat Analysis and Risk Assessment
Threat Analysis and Risk Assessment — TARA — is the analytical foundation of automotive cybersecurity. Required by ISO SAE 21434, referenced in UN R155/WP.29, and codified in the SAE J3061 guidebook, TARA is the process through which automotive organizations identify what can go wrong with a vehicle’s cybersecurity, how severe the consequences would be, and what needs to be done about it.
Yet TARA is also one of the most consistently underestimated activities in automotive development programs. Organizations that treat it as a documentation exercise — rather than a rigorous analytical process — produce compliance artifacts that fail to accurately characterize their threat landscape, leading to inadequate cybersecurity requirements, missed vulnerabilities, and regulatory exposure.
What Is TARA in the Context of ISO SAE 21434?
In ISO SAE 21434, TARA is formally defined in Clause 15 (Threat Analysis and Risk Assessment) and is required at the item level — meaning for every vehicle system or component that is within the cybersecurity scope of the development program. The TARA process produces three primary outputs: a list of threat scenarios (with associated damage scenarios), a risk assessment for each scenario, and cybersecurity goals that define acceptable risk levels.
These cybersecurity goals then drive the entire downstream engineering process: requirements, design constraints, implementation guidance, and test cases. A TARA that misses a significant threat scenario creates a blind spot that propagates through every subsequent engineering activity.
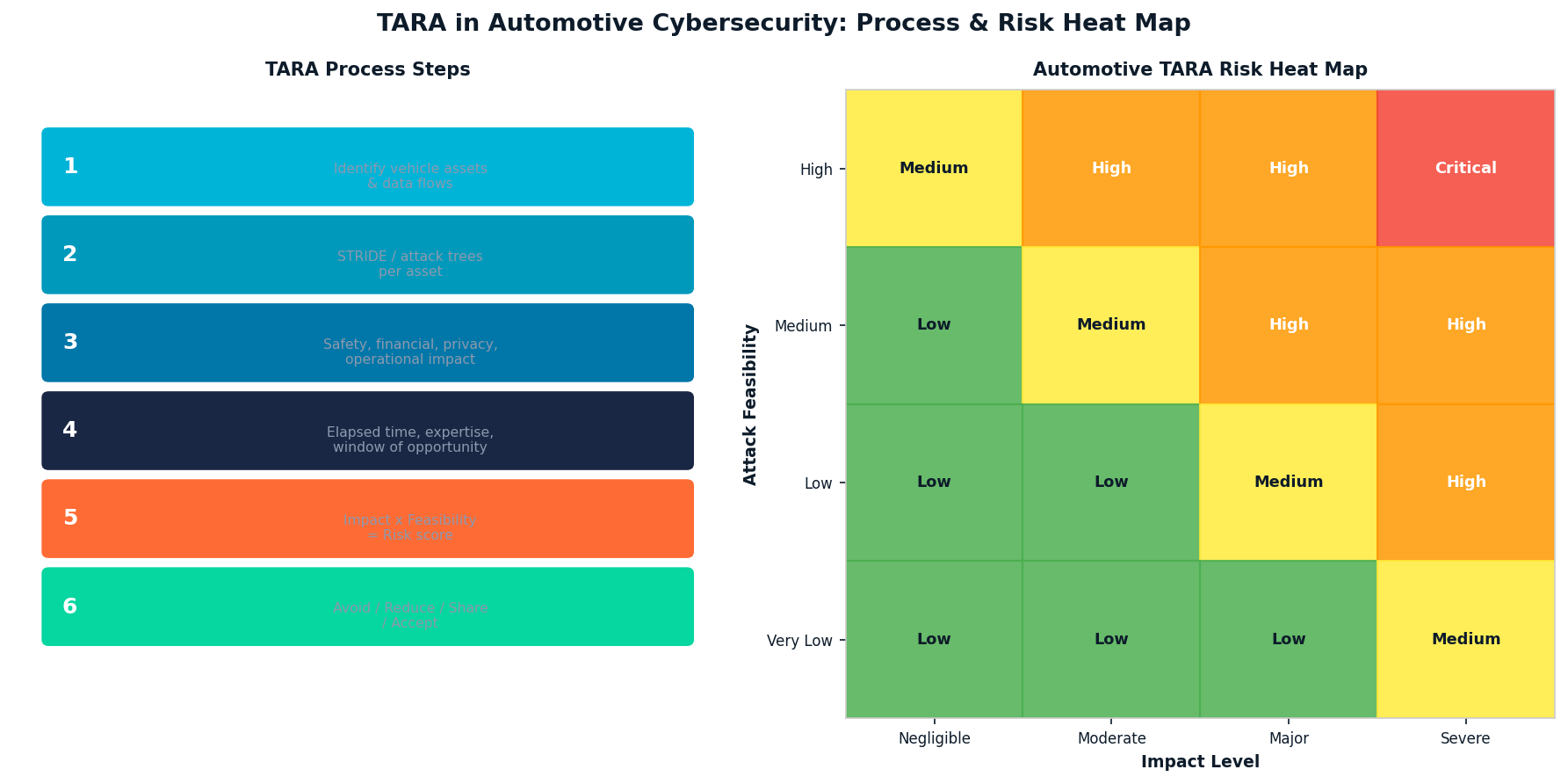
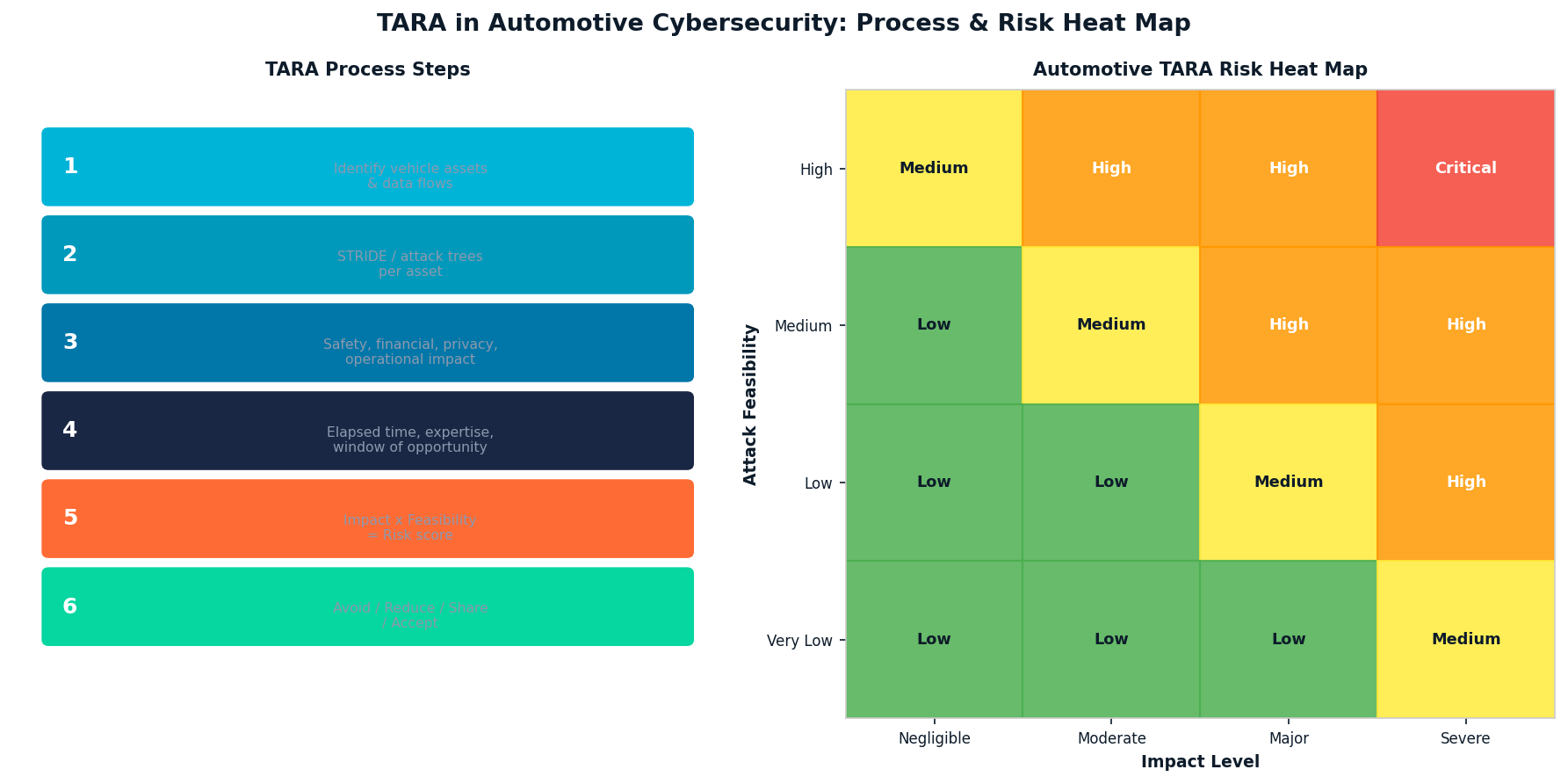
The Six Steps of Automotive TARA
| Step | Activity | Key Output |
| 1. Asset Identification | Identify vehicle assets, data, and functions | Asset register with cybersecurity relevance |
| 2. Threat Modeling | Enumerate threats per asset using STRIDE/attack trees | Threat scenario catalog |
| 3. Impact Assessment | Evaluate Safety, Financial, Operational, Privacy impact | Impact rating per scenario (1-4 scale) |
| 4. Attack Feasibility | Assess elapsed time, expertise, equipment, knowledge | Feasibility rating per threat |
| 5. Risk Determination | Combine impact and feasibility → risk value | Risk matrix with prioritization |
| 6. Risk Treatment | Define treatment: Avoid / Reduce / Share / Accept | Cybersecurity goals and treatment decisions |
STRIDE and Attack Trees: Core Threat Modeling Methods
ISO SAE 21434 does not mandate a specific threat modeling methodology, but STRIDE (Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, Elevation of Privilege) and attack trees are the most widely used approaches in automotive TARA practice. STRIDE provides a systematic taxonomy that ensures analysts consider all relevant threat categories across each asset. Attack trees enable complex multi-step attack sequences to be documented and analyzed, which is important for ECU-level threats where an attacker must chain multiple exploits to achieve their goal.
Impact Categories in Automotive TARA
| Impact Category | Examples | Severity Scale |
| Safety (S) | Physical harm to occupants, road users | S0 (no harm) to S3 (life-threatening) |
| Financial (F) | Warranty costs, recalls, liability | F0 to F3 (based on monetary threshold) |
| Operational (O) | Vehicle unavailability, function loss | O0 to O3 (based on scope of disruption) |
| Privacy (P) | Personal data exposure, tracking | P0 to P3 (per GDPR severity categories) |
TARA Automation: Why Manual Processes Fail at Scale
Modern vehicles contain 100+ ECUs communicating across multiple network domains. A single vehicle program may require TARA analyses for dozens of items and components, each with hundreds of potential threat scenarios. Performing this work manually in spreadsheets creates consistency problems, traceability gaps, and significant rework burden when designs change.
Automated TARA tools that maintain structured asset-threat-risk linkages, propagate design changes to affected analyses, and generate auditable compliance evidence reduce both cycle time and error rate by an order of magnitude compared to manual methods.
PlaxidityX’s Security AutoDesigner is purpose-built for automotive TARA automation, with structured support for ISO SAE 21434 Clause 15 processes, attack tree construction, and automatic traceability from threat scenarios to cybersecurity requirements. For a blog-level introduction to TARA in risk management, PlaxidityX’s guide to automating automotive cybersecurity risk management provides practical context.
TARA in the Supply Chain: Sharing and Integrating Analysis
A persistent challenge in automotive TARA is that OEMs and suppliers each perform analyses that must ultimately be consistent with each other. When an OEM’s TARA identifies a threat to a supplier-provided ECU, the supplier’s own TARA must either address that threat or explicitly accept the residual risk at the organizational interface. ISO SAE 21434 Clause 5 (Distributed Development) defines the contractual and technical obligations that govern this handoff.
Further Reading
The SAE J3061 cybersecurity guidebook provides the foundational threat modeling guidance that ISO SAE 21434 builds upon. For independent coverage of TARA methodology developments, AllTechNews on automotive cybersecurity analysis tracks industry practice and tooling.
Conclusion
TARA is not a one-time compliance activity — it is a living analytical process that must be maintained as vehicle designs evolve, new vulnerabilities are discovered, and threat landscapes shift. Organizations that invest in structured, automated TARA processes produce better security requirements, pass regulatory audits more efficiently, and build a genuine organizational memory of their cybersecurity risk posture across programs and generations of vehicles.
Business Solutions
Automotive IDS (Intrusion Detection Software): Safeguarding the Future of Connected Vehicles

The evolution of connected vehicles, autonomous driving systems, and over-the-air (OTA) updates has transformed the automotive industry into a high-tech environment. While these advancements offer numerous benefits, they also introduce new cybersecurity vulnerabilities. As modern vehicles become more complex and interconnected, the need to protect them from cyber-attacks becomes ever more urgent. One of the critical solutions to address these threats is the integration of Automotive Intrusion Detection Software (IDS Automotive).
Automotive IDS is designed to monitor vehicle systems in real-time, detect malicious activities, and respond to potential cybersecurity threats. In an era where vehicles are increasingly targeted by cybercriminals, an effective IDS plays a pivotal role in safeguarding not just the vehicle’s software and hardware, but also the safety of drivers, passengers, and other road users.
What is Automotive Intrusion Detection Software (IDS)?
Intrusion Detection Software (IDS) is a security technology that monitors and analyzes the activities of a system to detect signs of unauthorized access or suspicious behavior. In the context of automotive cybersecurity, IDS focuses on identifying and preventing attacks on a vehicle’s electronic control units (ECUs), communication networks, and other critical systems.
An automotive IDS typically operates by detecting irregularities in vehicle behavior that could indicate a cyberattack, such as unusual data traffic, unauthorized commands, or abnormal sensor readings. It analyzes the vehicle’s internal network traffic, such as Controller Area Network (CAN) bus, Ethernet, and FlexRay protocols, for any signs of intrusion or tampering.
How Automotive IDS Works
Automotive IDS operates in much the same way as traditional intrusion detection systems used in IT security, with some key differences specific to the automotive context:
1. Data Monitoring:
Automotive IDS continuously monitors the internal communication networks of a vehicle, including the CAN bus, Ethernet, and other communication channels. These networks serve as the backbone for data transmission between the vehicle’s various ECUs (e.g., engine control, infotainment, braking, steering), sensors, and actuators.
2. Anomaly Detection:
IDS systems typically use anomaly-based detection techniques to identify abnormal behavior in vehicle communication patterns. By establishing a baseline for “normal” vehicle behavior, the IDS can flag any activity that deviates from this baseline. Examples of anomalies could include unexpected changes in sensor readings, unusual messages between ECUs, or abnormal network traffic patterns that may indicate a cyberattack.
3. Signature-Based Detection:
Some IDS systems also use signature-based detection, which compares vehicle behavior against known attack signatures or pre-defined patterns of malicious activity. These signatures are updated regularly to reflect emerging threats, ensuring that the IDS can detect even the most recent attack methods.
4. Response Mechanisms:
Upon detecting a potential intrusion or anomaly, the IDS can trigger predefined responses to mitigate the threat. This may involve logging the event for further investigation, sending alerts to the vehicle’s central control unit, or taking immediate action such as isolating affected ECUs or triggering a failsafe mode to ensure safety.
5. Integration with Vehicle Security Systems:
An automotive IDS is typically integrated with other vehicle security systems, such as firewalls, secure communication protocols, and encryption mechanisms. This multi-layered security approach enhances the vehicle’s ability to prevent, detect, and respond to cyber threats.

Why is Automotive IDS Important?
The importance of Automotive IDS cannot be overstated in today’s connected car ecosystem. The integration of increasingly sophisticated technologies, like Advanced Driver Assistance Systems (ADAS) and autonomous driving features, has expanded the attack surface for potential cybercriminals. Here are several reasons why Automotive IDS is crucial:
1. Protecting Critical Vehicle Functions:
Modern vehicles are highly dependent on complex electronic systems to manage safety-critical functions, such as braking, steering, and acceleration. A successful cyberattack on these systems could have catastrophic consequences. Automotive IDS helps prevent unauthorized access to these systems by detecting and responding to potential threats in real-time.
2. Early Detection of Cyber Threats:
Intrusion detection software is one of the best tools for identifying cyberattacks before they can do significant damage. Whether it’s a remote hacker attempting to gain control of a vehicle’s systems or a local attacker trying to exploit vulnerabilities, an IDS can alert the vehicle’s control systems to the presence of an attack, enabling timely countermeasures.
3. Mitigating Risks to Privacy:
Connected vehicles gather and share vast amounts of data, from GPS locations to personal preferences. Cybercriminals may target these data streams to compromise users’ privacy. Automotive IDS helps prevent data breaches by identifying suspicious activity on the vehicle’s communication channels.
4. Real-Time Monitoring and Response:
In contrast to traditional vehicle security solutions, which may only provide post-event analysis, IDS operates in real-time. This means that a vehicle’s security systems can immediately detect and respond to an ongoing attack, minimizing the potential damage and ensuring that the vehicle remains operational and safe.
5. Compliance with Regulatory Standards:
The automotive industry is subject to increasing regulatory scrutiny related to cybersecurity, including standards like ISO/SAE 21434 for automotive cybersecurity and the UN R155 regulation for vehicle cyber resilience. Implementing Automotive IDS can help manufacturers meet these regulatory requirements and demonstrate their commitment to vehicle safety and security.
Types of Automotive IDS
There are two main types of IDS that can be used in automotive cybersecurity:
1. Host-Based IDS (HIDS):
Host-based IDS operates on individual ECUs or control units within the vehicle. These systems monitor the specific behaviors of the vehicle’s hardware and software to detect intrusions. HIDS can track file integrity, system configurations, and application behavior, providing detailed insights into any changes that could indicate an attack.
2. Network-Based IDS (NIDS):
Network-based IDS monitors the vehicle’s communication networks, such as CAN and Ethernet, to detect unauthorized or suspicious network traffic. NIDS analyzes the flow of messages between ECUs, sensors, and other vehicle components, looking for signs of malicious activity or abnormal data exchanges.
In many cases, an automotive cybersecurity system will use a combination of both HIDS and NIDS to provide comprehensive coverage against cyber threats.
Challenges in Implementing Automotive IDS
While the benefits of automotive IDS are clear, the implementation of these systems comes with its own set of challenges:
1. Complex Vehicle Architectures:
Modern vehicles contain a vast array of ECUs, sensors, and communication networks, each with unique security needs. Designing an IDS system that can effectively monitor and protect all these components is complex and requires integration with the vehicle’s entire electronic ecosystem.
2. Real-Time Processing:
Given the critical nature of vehicle operations, IDS systems must be able to detect threats in real-time without causing delays or performance degradation. This requires high processing power and advanced algorithms capable of handling large amounts of data quickly and efficiently.
3. False Positives:
One of the challenges with any IDS system is minimizing false positives — situations where benign activity is mistakenly flagged as malicious. In automotive contexts, false positives can be particularly problematic, as they may cause unnecessary disruptions to vehicle operations or trigger incorrect safety measures.
4. Evolving Cyber Threats:
The cybersecurity landscape is constantly evolving, with new attack methods and vulnerabilities emerging regularly. Automotive IDS systems need to be updated continuously to stay ahead of these threats. This can require ongoing development and support to ensure that vehicles remain secure over time.
As the automotive industry embraces the future of connectivity and automation, the need for robust cybersecurity measures has never been more critical. Automotive Intrusion Detection Software (IDS) serves as a vital component in safeguarding vehicles from the growing threat of cyber-attacks. By detecting and mitigating potential intrusions in real-time, IDS helps protect not only vehicle safety and privacy but also the reputation of manufacturers in an increasingly security-conscious market. As automotive technology continues to advance, the role of IDS in ensuring the integrity of connected and autonomous vehicles will only become more important.
-

 Business Solutions2 years ago
Business Solutions2 years agoLive Video Broadcasting with Bonded Transmission Technology
-

 Business Solutions11 months ago
Business Solutions11 months agoThe Future of Healthcare SMS and RCS Messaging
-

 Business Solutions2 years ago
Business Solutions2 years ago2-Way Texting Solutions from Company Message Services
-

 Business Solutions2 years ago
Business Solutions2 years agoCommunication with Analog to Fiber Converters & RF Link Budgets
-

 DSRC Communication1 year ago
DSRC Communication1 year agoThe Crossroads of Connectivity: DSRC vs. C-V2X Technologies in Automotive Communication
-
Electronics2 years ago
AI Modules and Smart Home Chips: Future of Home Automation
-
 Tech3 years ago
Tech3 years agoThe Symphony of Connectivity: Understanding Ethernet Devices
-

 Business Solutions2 years ago
Business Solutions2 years agoWholesale SMS Platforms with OTP Services







