Cybersecurity
A Responsible Approach Towards Cyber Breach Mitigation
Data security is a serious issue faced by businesses across various industries. Hackers are constantly probing corporate networks, looking for vulnerabilities in the system so that they can gain access to sensitive information.
Every year, millions of sensitive data are reported to be exploited by cyber attackers. The security team needs to imbibe comprehensive cyber breach mitigation processes in order to reduce the risk associated with them.
What is Cyber Breach?
Cyber breach is different from cybersecurity attacks. A cyber breach is an incident in which a person’s name, social security number, medical records, financial records, driver’s license number, etc. are at risk due to public exposure. Basically, in such incidents, confidential information is stolen from the system.
Such breaches can prove to be detrimental for both individuals as well as businesses. Companies store a lot of personal information about their customers that can be exposed. Such incidents can result in loss of existing business, the trust of customers, lawsuits encompassing hefty fines, etc.
The direct and indirect loss of such security cases can account for millions of dollars. This is why companies need to have a proper cyber breach mitigation plan in place.
How to Prevent the Occurrence of Cyber Breach?
Encrypted storage, as well as multi-factor authentication, are the basic steps followed by cyber breach mitigation services to reinforce the security measures. Additionally, 24*7, real-time monitoring is imperative to prevent cyber breaches. Organizations can protect their systems from breaches if they are able to see their environment from all possible angles and at all the time.
This is why relying on cyber breach mitigation services is a good option. These service providers integrated automated tools and latest technologies to mitigate the chances of risks and boost the incident response. Moreover, the expertise of your security staff also plays an important role in the quality of your overall system.
Organizations should invest in regular training programs so that the employees are updated with the latest policies, security standards, and expectations.
Process of Cyber Breach Mitigation and Incident Response
In case of a breach, certain proactive measures can mitigate and contain the damage. The main focus should be to block the flow and additional loss of data by determining the vulnerabilities and fixing the same instantly. Following are the steps that will help in this process –
1. Set-Up an Expert Response Team
An organization should have a response team, including experts from legal, forensic, IT, operations, HR, communications, management, and investor relations departments. These teams will together deal with the aftermath of breach across different areas of the business.
2. Securing the Infrastructure
When stemming the loss, the team needs to secure the physical business area along with its systems. All the business equipment should be taken offline or if needed, replaced. Experts should monitor access to the logical and physical environment.
And, depending on the severity of the situation should be frozen. All the passwords and access codes for the users should be immediately updated.
3. Eliminate the Vulnerability
Forensic experts should assess the network segmentation and check who gained access to what by leveraging the data from SIEM logs and agents. This step may help you discover the root cause of the issue. Review whether or not proper procedures and technologies were in place and check out the access logs for any traces.
Additionally, vulnerabilities may arise from third-party providers as well. Therefore, it is important that you authenticate the data, systems, and applications that were compromised and determine the degree of damage. Contact the stakeholders to inform them of the breach and what necessary steps are being taken to recover.
4. Set-Up A Clear Communication Plan
When working on cyber breach mitigation, the importance of clear and transparent communication cannot be overlooked. Instead of covering up the breach, as many companies have done previously, take a transparent approach.
Include all the stakeholders in your mitigation plan that include investors, business partners, employees, and customers. Inform them about the incident without giving away too much information. Moreover, report the breach to law enforcement and adhere to the relevant state and federal guidelines.
The cyber breach mitigation process is not about covering the incident; instead, it is centered around taking a responsible approach to mitigate the damage caused by the attack.
Cybersecurity
TARA in Automotive Cybersecurity: A Complete Guide to Threat Analysis and Risk Assessment
Threat Analysis and Risk Assessment — TARA — is the analytical foundation of automotive cybersecurity. Required by ISO SAE 21434, referenced in UN R155/WP.29, and codified in the SAE J3061 guidebook, TARA is the process through which automotive organizations identify what can go wrong with a vehicle’s cybersecurity, how severe the consequences would be, and what needs to be done about it.
Yet TARA is also one of the most consistently underestimated activities in automotive development programs. Organizations that treat it as a documentation exercise — rather than a rigorous analytical process — produce compliance artifacts that fail to accurately characterize their threat landscape, leading to inadequate cybersecurity requirements, missed vulnerabilities, and regulatory exposure.
What Is TARA in the Context of ISO SAE 21434?
In ISO SAE 21434, TARA is formally defined in Clause 15 (Threat Analysis and Risk Assessment) and is required at the item level — meaning for every vehicle system or component that is within the cybersecurity scope of the development program. The TARA process produces three primary outputs: a list of threat scenarios (with associated damage scenarios), a risk assessment for each scenario, and cybersecurity goals that define acceptable risk levels.
These cybersecurity goals then drive the entire downstream engineering process: requirements, design constraints, implementation guidance, and test cases. A TARA that misses a significant threat scenario creates a blind spot that propagates through every subsequent engineering activity.
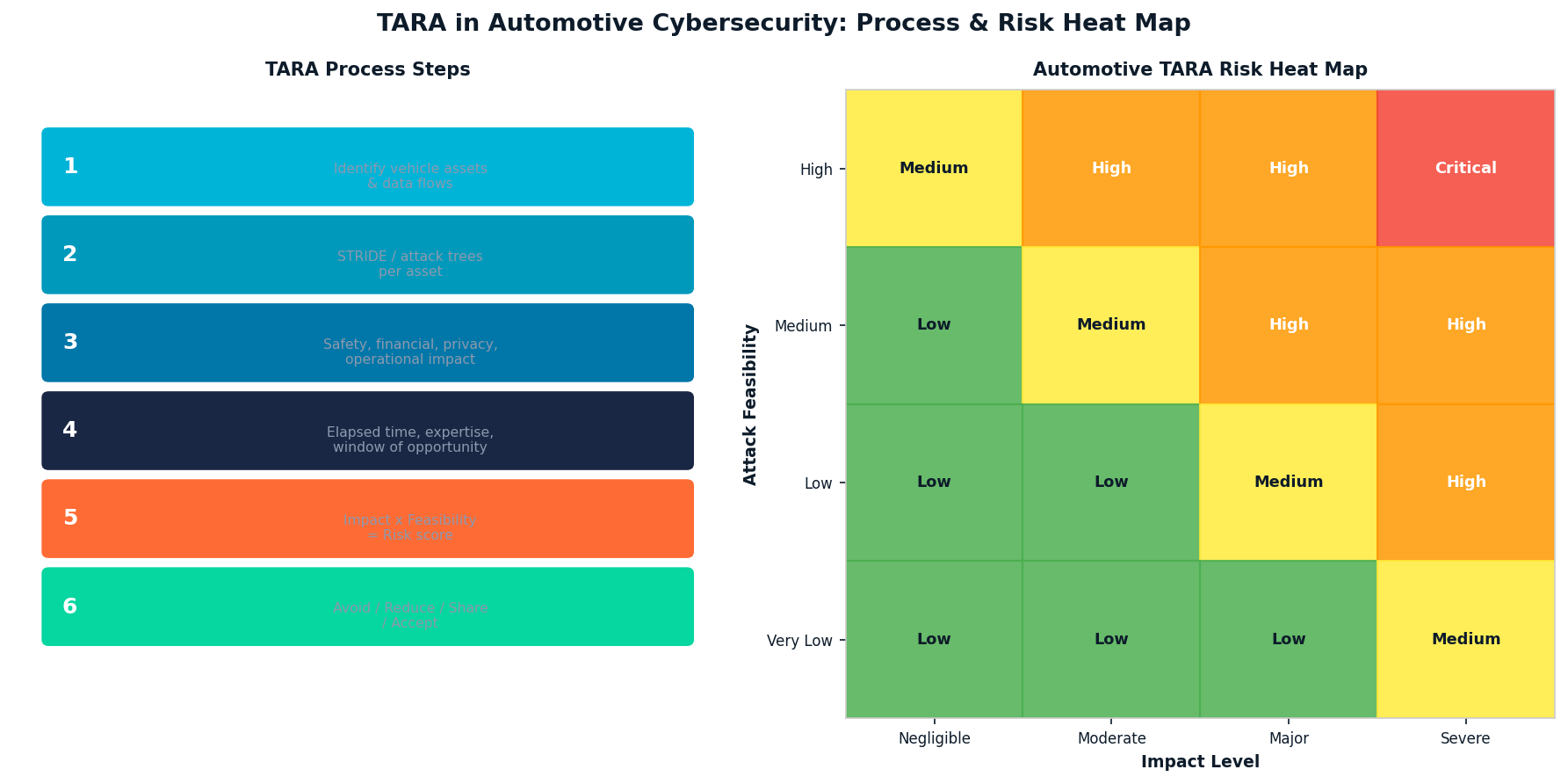
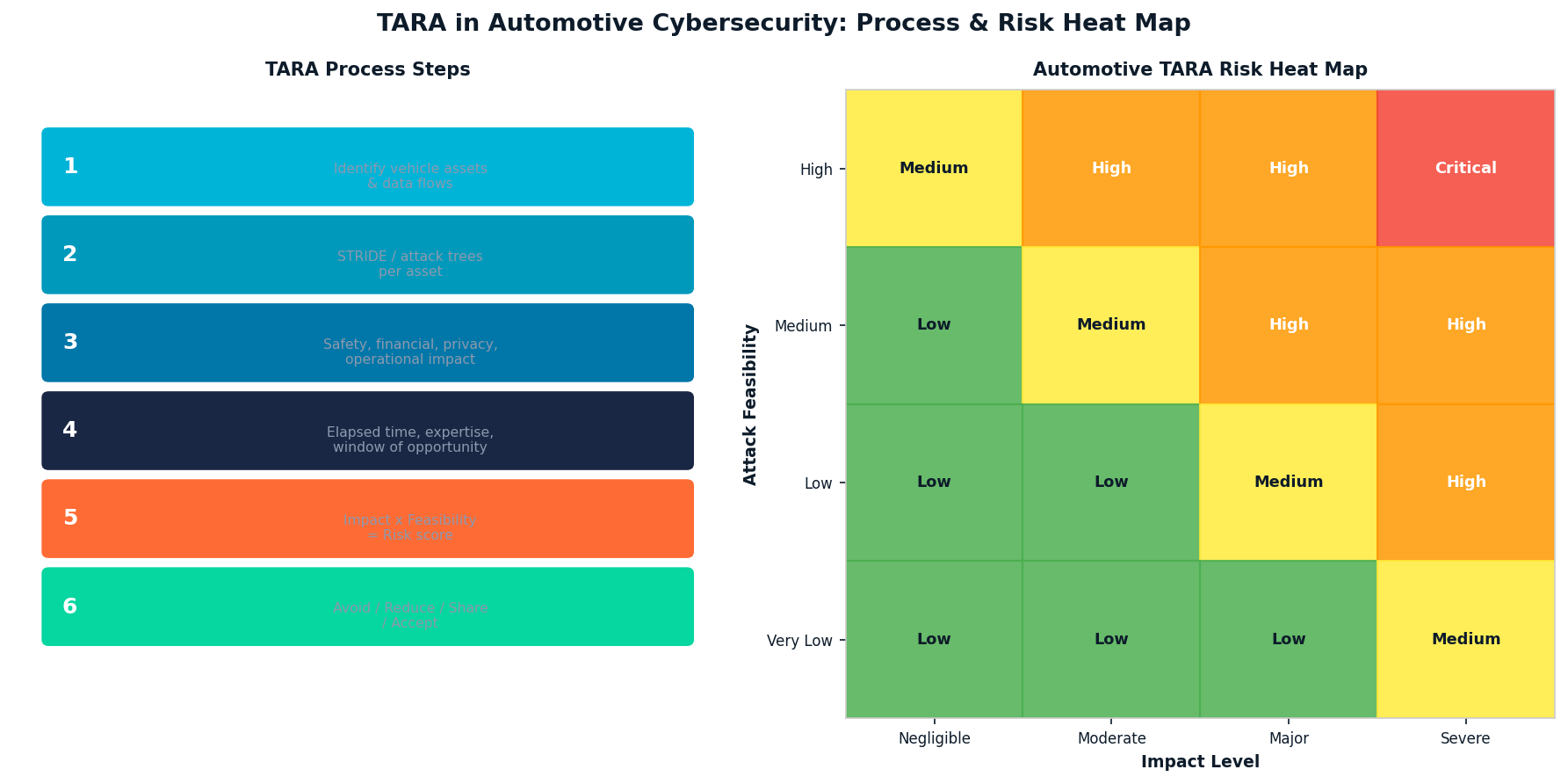
The Six Steps of Automotive TARA
| Step | Activity | Key Output |
| 1. Asset Identification | Identify vehicle assets, data, and functions | Asset register with cybersecurity relevance |
| 2. Threat Modeling | Enumerate threats per asset using STRIDE/attack trees | Threat scenario catalog |
| 3. Impact Assessment | Evaluate Safety, Financial, Operational, Privacy impact | Impact rating per scenario (1-4 scale) |
| 4. Attack Feasibility | Assess elapsed time, expertise, equipment, knowledge | Feasibility rating per threat |
| 5. Risk Determination | Combine impact and feasibility → risk value | Risk matrix with prioritization |
| 6. Risk Treatment | Define treatment: Avoid / Reduce / Share / Accept | Cybersecurity goals and treatment decisions |
STRIDE and Attack Trees: Core Threat Modeling Methods
ISO SAE 21434 does not mandate a specific threat modeling methodology, but STRIDE (Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, Elevation of Privilege) and attack trees are the most widely used approaches in automotive TARA practice. STRIDE provides a systematic taxonomy that ensures analysts consider all relevant threat categories across each asset. Attack trees enable complex multi-step attack sequences to be documented and analyzed, which is important for ECU-level threats where an attacker must chain multiple exploits to achieve their goal.
Impact Categories in Automotive TARA
| Impact Category | Examples | Severity Scale |
| Safety (S) | Physical harm to occupants, road users | S0 (no harm) to S3 (life-threatening) |
| Financial (F) | Warranty costs, recalls, liability | F0 to F3 (based on monetary threshold) |
| Operational (O) | Vehicle unavailability, function loss | O0 to O3 (based on scope of disruption) |
| Privacy (P) | Personal data exposure, tracking | P0 to P3 (per GDPR severity categories) |
TARA Automation: Why Manual Processes Fail at Scale
Modern vehicles contain 100+ ECUs communicating across multiple network domains. A single vehicle program may require TARA analyses for dozens of items and components, each with hundreds of potential threat scenarios. Performing this work manually in spreadsheets creates consistency problems, traceability gaps, and significant rework burden when designs change.
Automated TARA tools that maintain structured asset-threat-risk linkages, propagate design changes to affected analyses, and generate auditable compliance evidence reduce both cycle time and error rate by an order of magnitude compared to manual methods.
PlaxidityX’s Security AutoDesigner is purpose-built for automotive TARA automation, with structured support for ISO SAE 21434 Clause 15 processes, attack tree construction, and automatic traceability from threat scenarios to cybersecurity requirements. For a blog-level introduction to TARA in risk management, PlaxidityX’s guide to automating automotive cybersecurity risk management provides practical context.
TARA in the Supply Chain: Sharing and Integrating Analysis
A persistent challenge in automotive TARA is that OEMs and suppliers each perform analyses that must ultimately be consistent with each other. When an OEM’s TARA identifies a threat to a supplier-provided ECU, the supplier’s own TARA must either address that threat or explicitly accept the residual risk at the organizational interface. ISO SAE 21434 Clause 5 (Distributed Development) defines the contractual and technical obligations that govern this handoff.
Further Reading
The SAE J3061 cybersecurity guidebook provides the foundational threat modeling guidance that ISO SAE 21434 builds upon. For independent coverage of TARA methodology developments, AllTechNews on automotive cybersecurity analysis tracks industry practice and tooling.
Conclusion
TARA is not a one-time compliance activity — it is a living analytical process that must be maintained as vehicle designs evolve, new vulnerabilities are discovered, and threat landscapes shift. Organizations that invest in structured, automated TARA processes produce better security requirements, pass regulatory audits more efficiently, and build a genuine organizational memory of their cybersecurity risk posture across programs and generations of vehicles.
Business Solutions
Automotive IDS (Intrusion Detection Software): Safeguarding the Future of Connected Vehicles

The evolution of connected vehicles, autonomous driving systems, and over-the-air (OTA) updates has transformed the automotive industry into a high-tech environment. While these advancements offer numerous benefits, they also introduce new cybersecurity vulnerabilities. As modern vehicles become more complex and interconnected, the need to protect them from cyber-attacks becomes ever more urgent. One of the critical solutions to address these threats is the integration of Automotive Intrusion Detection Software (IDS Automotive).
Automotive IDS is designed to monitor vehicle systems in real-time, detect malicious activities, and respond to potential cybersecurity threats. In an era where vehicles are increasingly targeted by cybercriminals, an effective IDS plays a pivotal role in safeguarding not just the vehicle’s software and hardware, but also the safety of drivers, passengers, and other road users.
What is Automotive Intrusion Detection Software (IDS)?
Intrusion Detection Software (IDS) is a security technology that monitors and analyzes the activities of a system to detect signs of unauthorized access or suspicious behavior. In the context of automotive cybersecurity, IDS focuses on identifying and preventing attacks on a vehicle’s electronic control units (ECUs), communication networks, and other critical systems.
An automotive IDS typically operates by detecting irregularities in vehicle behavior that could indicate a cyberattack, such as unusual data traffic, unauthorized commands, or abnormal sensor readings. It analyzes the vehicle’s internal network traffic, such as Controller Area Network (CAN) bus, Ethernet, and FlexRay protocols, for any signs of intrusion or tampering.
How Automotive IDS Works
Automotive IDS operates in much the same way as traditional intrusion detection systems used in IT security, with some key differences specific to the automotive context:
1. Data Monitoring:
Automotive IDS continuously monitors the internal communication networks of a vehicle, including the CAN bus, Ethernet, and other communication channels. These networks serve as the backbone for data transmission between the vehicle’s various ECUs (e.g., engine control, infotainment, braking, steering), sensors, and actuators.
2. Anomaly Detection:
IDS systems typically use anomaly-based detection techniques to identify abnormal behavior in vehicle communication patterns. By establishing a baseline for “normal” vehicle behavior, the IDS can flag any activity that deviates from this baseline. Examples of anomalies could include unexpected changes in sensor readings, unusual messages between ECUs, or abnormal network traffic patterns that may indicate a cyberattack.
3. Signature-Based Detection:
Some IDS systems also use signature-based detection, which compares vehicle behavior against known attack signatures or pre-defined patterns of malicious activity. These signatures are updated regularly to reflect emerging threats, ensuring that the IDS can detect even the most recent attack methods.
4. Response Mechanisms:
Upon detecting a potential intrusion or anomaly, the IDS can trigger predefined responses to mitigate the threat. This may involve logging the event for further investigation, sending alerts to the vehicle’s central control unit, or taking immediate action such as isolating affected ECUs or triggering a failsafe mode to ensure safety.
5. Integration with Vehicle Security Systems:
An automotive IDS is typically integrated with other vehicle security systems, such as firewalls, secure communication protocols, and encryption mechanisms. This multi-layered security approach enhances the vehicle’s ability to prevent, detect, and respond to cyber threats.

Why is Automotive IDS Important?
The importance of Automotive IDS cannot be overstated in today’s connected car ecosystem. The integration of increasingly sophisticated technologies, like Advanced Driver Assistance Systems (ADAS) and autonomous driving features, has expanded the attack surface for potential cybercriminals. Here are several reasons why Automotive IDS is crucial:
1. Protecting Critical Vehicle Functions:
Modern vehicles are highly dependent on complex electronic systems to manage safety-critical functions, such as braking, steering, and acceleration. A successful cyberattack on these systems could have catastrophic consequences. Automotive IDS helps prevent unauthorized access to these systems by detecting and responding to potential threats in real-time.
2. Early Detection of Cyber Threats:
Intrusion detection software is one of the best tools for identifying cyberattacks before they can do significant damage. Whether it’s a remote hacker attempting to gain control of a vehicle’s systems or a local attacker trying to exploit vulnerabilities, an IDS can alert the vehicle’s control systems to the presence of an attack, enabling timely countermeasures.
3. Mitigating Risks to Privacy:
Connected vehicles gather and share vast amounts of data, from GPS locations to personal preferences. Cybercriminals may target these data streams to compromise users’ privacy. Automotive IDS helps prevent data breaches by identifying suspicious activity on the vehicle’s communication channels.
4. Real-Time Monitoring and Response:
In contrast to traditional vehicle security solutions, which may only provide post-event analysis, IDS operates in real-time. This means that a vehicle’s security systems can immediately detect and respond to an ongoing attack, minimizing the potential damage and ensuring that the vehicle remains operational and safe.
5. Compliance with Regulatory Standards:
The automotive industry is subject to increasing regulatory scrutiny related to cybersecurity, including standards like ISO/SAE 21434 for automotive cybersecurity and the UN R155 regulation for vehicle cyber resilience. Implementing Automotive IDS can help manufacturers meet these regulatory requirements and demonstrate their commitment to vehicle safety and security.
Types of Automotive IDS
There are two main types of IDS that can be used in automotive cybersecurity:
1. Host-Based IDS (HIDS):
Host-based IDS operates on individual ECUs or control units within the vehicle. These systems monitor the specific behaviors of the vehicle’s hardware and software to detect intrusions. HIDS can track file integrity, system configurations, and application behavior, providing detailed insights into any changes that could indicate an attack.
2. Network-Based IDS (NIDS):
Network-based IDS monitors the vehicle’s communication networks, such as CAN and Ethernet, to detect unauthorized or suspicious network traffic. NIDS analyzes the flow of messages between ECUs, sensors, and other vehicle components, looking for signs of malicious activity or abnormal data exchanges.
In many cases, an automotive cybersecurity system will use a combination of both HIDS and NIDS to provide comprehensive coverage against cyber threats.
Challenges in Implementing Automotive IDS
While the benefits of automotive IDS are clear, the implementation of these systems comes with its own set of challenges:
1. Complex Vehicle Architectures:
Modern vehicles contain a vast array of ECUs, sensors, and communication networks, each with unique security needs. Designing an IDS system that can effectively monitor and protect all these components is complex and requires integration with the vehicle’s entire electronic ecosystem.
2. Real-Time Processing:
Given the critical nature of vehicle operations, IDS systems must be able to detect threats in real-time without causing delays or performance degradation. This requires high processing power and advanced algorithms capable of handling large amounts of data quickly and efficiently.
3. False Positives:
One of the challenges with any IDS system is minimizing false positives — situations where benign activity is mistakenly flagged as malicious. In automotive contexts, false positives can be particularly problematic, as they may cause unnecessary disruptions to vehicle operations or trigger incorrect safety measures.
4. Evolving Cyber Threats:
The cybersecurity landscape is constantly evolving, with new attack methods and vulnerabilities emerging regularly. Automotive IDS systems need to be updated continuously to stay ahead of these threats. This can require ongoing development and support to ensure that vehicles remain secure over time.
As the automotive industry embraces the future of connectivity and automation, the need for robust cybersecurity measures has never been more critical. Automotive Intrusion Detection Software (IDS) serves as a vital component in safeguarding vehicles from the growing threat of cyber-attacks. By detecting and mitigating potential intrusions in real-time, IDS helps protect not only vehicle safety and privacy but also the reputation of manufacturers in an increasingly security-conscious market. As automotive technology continues to advance, the role of IDS in ensuring the integrity of connected and autonomous vehicles will only become more important.
Cybersecurity
Cybersecurity venture capital
There are many ways to guard against cyberattacks, but as the number of malicious programs and attacks continues to grow, more companies are investing in cybersecurity venture capital. Find out what some of the benefits of investing in this type of funding is, and how you can find a company that will be a good fit for your company’s needs.
Technology has revolutionized how we live, and work, and nowhere is that more apparent than in the world of cybersecurity. In just a few short years, cybersecurity has gone from a niche to a booming sector, with startups and established companies vying for a piece of the pie. One of the key drivers of this growth has been venture capital investment. Cybersecurity venture capitalists have poured billions of dollars into promising startups, helping them to bring their products to market and scale their businesses. In this blog post, we will look at the role of venture capital in the cybersecurity industry and some of the most prominent investors in the space. We will also explore some of the challenges that startups face when trying to raise funding and how VCs are helping to address these issues.

cybersecurity venture capital firms
Several cybersecurity venture capital firms invest in early-stage companies. These firms typically focus on companies developing innovative technologies to address the growing cyber security threats faced by businesses and individuals.
Some of the leading cybersecurity venture capital firms include:
* Accel Partners
* Bessemer Venture Partners
* Google Ventures
* Kleiner Perkins Caufield & Byers
* New Enterprise Associates
* Sequoia Capital
* Elron Venture
These firms have invested in several well-known cybersecurity startups, including:
* CrowdStrike: A leader in endpoint security, CrowdStrike has raised over $200 million from investors such as Accel Partners, Google Ventures, and Warburg Pincus.
* Palo Alto Networks: A provider of network security solutions, Palo Alto Networks has raised over $1 billion from investors such as Sequoia Capital, Fidelity Investments, and Mayfield Fund.
* Symantec: A global leader in cyber security, Symantec has raised over $5 billion from investors such as TPG Capital, Silver Lake Partners, and Bain Capital.
Who is the best venture capitalist
As the number of cyberattacks continues to grow, more companies are looking for ways to protect themselves. One way to do this is to invest in cybersecurity venture capital. But who is the best venture capitalist?
There are a lot of different factors to consider when it comes to choosing a venture capitalist. One crucial factor is track record. You want to look for a venture capitalist with a proven track record of investing in successful companies. Another factor to consider is experience. Look for a venture capitalist who has experience working with startups in the cybersecurity industry.
Another essential factor to consider is the amount of money that the venture capitalist has to invest. You want to seek a venture capitalist with deep pockets who can fund your startup to grow and scale.
Finally, you want to look for a venture capitalist who shares your vision for the company. This is someone who believes in your product or service and wants to help you grow your business. When you find a venture capitalist who meets all of these criteria, you know you’ve found someone who can help take your startup to the next level.
Cybersecurity VC Funding Rolls On In 2022
As we move into the new year, it’s clear that cybersecurity is still a top priority for businesses and organizations worldwide. And as such, venture capitalists are still pumping money into the space.
In fact, according to CB Insights, VC funding for cybersecurity startups hit a new high in 2020, with $10.9 billion invested across 437 deals. And they believe that this trend will continue in 2021 and beyond.
If you’re considering starting a cybersecurity company or are already running one and looking for funding, it’s worth considering the VC route. Here are a few things to keep in mind:
- There’s a lot of interest in cybersecurity right now: As mentioned above, VCs are still very interested in investing in cybersecurity companies. This is because there’s a growing awareness of the importance of cybersecurity and an increasing number of cyber threats.
- You need a strong team: As with any startup, having a solid team is essential for success. But it’s critical to cybersecurity because investors want to see that you have the right mix of technical and business skills. They also want to know that your team is passionate about what they’re doing and that they have the drive to succeed.
- Your product must be differentiated: With so many companies competing for attention in the cybersecurity space, your product must stand out from the crowd. It
-

 Business Solutions2 years ago
Business Solutions2 years agoLive Video Broadcasting with Bonded Transmission Technology
-

 Business Solutions11 months ago
Business Solutions11 months agoThe Future of Healthcare SMS and RCS Messaging
-

 Business Solutions2 years ago
Business Solutions2 years ago2-Way Texting Solutions from Company Message Services
-

 Business Solutions2 years ago
Business Solutions2 years agoCommunication with Analog to Fiber Converters & RF Link Budgets
-

 DSRC Communication1 year ago
DSRC Communication1 year agoThe Crossroads of Connectivity: DSRC vs. C-V2X Technologies in Automotive Communication
-
Electronics2 years ago
AI Modules and Smart Home Chips: Future of Home Automation
-
 Tech3 years ago
Tech3 years agoThe Symphony of Connectivity: Understanding Ethernet Devices
-

 Business Solutions2 years ago
Business Solutions2 years agoWholesale SMS Platforms with OTP Services







