Business Solutions
The Role of Secure SMS in Financial Services
In today’s fast-paced financial landscape, ensuring the privacy and security of sensitive information is paramount. As cyber threats become increasingly sophisticated, the financial sector faces the daunting challenge of protecting its most valuable asset: data. Enter Secure SMS, a powerful tool that is redefining secure communication. This innovative solution not only fortifies the walls against potential breaches but also facilitates seamless and reliable transactions. Imagine a world where every financial message is encrypted and guarded, ensuring that your private information remains just that—private. Dive into our exploration of how Secure SMS is revolutionizing the financial services industry, making it safer and more efficient than ever before.

Financial institutions rely heavily on SMS to interact with customers, whether it’s for sending transaction alerts, delivering one-time passwords (OTPs), or notifying clients of account activities. However, the rise of cyber threats has highlighted the need for secure SMS in financial SMS transactions. Ensuring that these communications are protected from unauthorized access is critical to maintaining customer trust and safeguarding sensitive financial information. This article will delve into the importance of secure SMS, the challenges it addresses, and best practices for implementing it in financial services.
Understanding Secure SMS
Secure SMS refers to the use of encryption and other security measures to protect SMS messages from interception and unauthorized access. Unlike regular SMS, which can be vulnerable to various forms of cyberattacks such as phishing, SIM swapping, and man-in-the-middle attacks, secure SMS ensures that the content of the message remains confidential between the sender and the recipient.
Encryption is a core component of secure SMS. It works by converting the message content into a coded format that can only be decoded by the intended recipient using a specific decryption key. This prevents attackers from reading the message even if they manage to intercept it during transmission. Secure SMS may also include additional features such as message authentication, which verifies the identity of the sender, and integrity checks to ensure that the message has not been altered.
In the financial sector, where the confidentiality and integrity of communications are paramount, secure SMS provides a critical layer of protection. It helps prevent unauthorized access to sensitive financial data and ensures that customers can trust the messages they receive from their banks or financial service providers.

The Role of Financial SMS in Modern Banking
Financial SMS is a vital tool for modern banking, providing customers with real-time updates and facilitating secure interactions between financial institutions and their clients. Common uses of financial SMS include transaction alerts, balance notifications, fraud detection warnings, and delivery of OTPs for two-factor authentication (2FA).
For example, when a customer makes a purchase or a transfer, the bank can instantly send a transaction alert via SMS, informing the customer of the activity on their account. This immediate notification allows customers to quickly spot any unauthorized transactions and take action to protect their accounts. Similarly, financial SMS is used to send OTPs, which are required to complete certain transactions or to log in to online banking platforms, adding an extra layer of security.
The convenience and immediacy of financial SMS make it an essential communication channel in banking. It keeps customers informed and engaged with their financial activities, while also enhancing the overall security of online transactions.
Why Security is Paramount in Financial SMS
The security of financial SMS is paramount because these messages often contain sensitive information that, if intercepted, could be exploited by cybercriminals. For instance, if an SMS containing a transaction alert or an OTP is intercepted, the attacker could potentially gain access to the customer’s financial accounts or use the information for fraudulent activities.
The risks associated with unsecured SMS in financial transactions are significant. Cybercriminals have developed various methods to intercept SMS messages, such as SIM swapping, where they convince a mobile carrier to transfer a customer’s phone number to a new SIM card controlled by the attacker. Once they have control of the number, they can receive all SMS messages intended for the victim, including OTPs and transaction alerts.
There have been several high-profile cases of SMS security breaches in the financial sector. For example, in 2019, hackers used SIM swapping to steal millions of dollars from cryptocurrency accounts by intercepting SMS-based two-factor authentication codes. Such incidents underscore the importance of implementing secure SMS to protect both the financial institutions and their customers from potential losses and reputational damage.
Implementing Secure SMS in Financial Services
Implementing secure SMS in financial services involves adopting best practices and using the right tools and technologies to ensure that all SMS communications are protected. Here are some key strategies for securing financial SMS:
- End-to-End Encryption: Ensure that all SMS messages are encrypted from the moment they are sent until they are received. This prevents unauthorized parties from accessing the content of the messages even if they are intercepted.
- Use of Secure Gateways: Partner with SMS service providers that offer secure messaging gateways, which provide additional layers of security, such as encrypted transmission channels and robust authentication mechanisms.
- Two-Factor Authentication (2FA): Implement 2FA for all critical financial transactions and account access. Secure SMS can be used to deliver OTPs that are required for verifying the identity of the user before allowing the transaction to proceed.
- Regular Security Audits: Conduct regular security audits of your SMS systems and protocols to identify potential vulnerabilities and ensure that all security measures are up to date with the latest industry standards.
- Educating Customers: Educate customers on the importance of SMS security and encourage them to report any suspicious activity, such as receiving unexpected OTPs or transaction alerts. Provide clear guidance on how they can protect their SMS communications, such as not sharing OTPs or sensitive information via SMS.
By implementing these practices, financial institutions can significantly reduce the risks associated with financial SMS and provide their customers with a secure and reliable communication channel.
Compliance and Regulations for Financial SMS
Financial SMS communications are subject to various regulatory requirements designed to protect consumer data and ensure the integrity of financial transactions. Compliance with these regulations is critical for financial institutions to avoid legal penalties and maintain customer trust.
One of the key regulations governing financial SMS is the General Data Protection Regulation (GDPR) in the European Union, which requires organizations to protect personal data and ensure the privacy of communications. Under GDPR, financial institutions must implement appropriate security measures, such as encryption, to protect SMS communications containing personal or financial information.
In the United States, the Federal Financial Institutions Examination Council (FFIEC) provides guidelines on electronic banking security, including the use of SMS for authentication and transaction alerts. Financial institutions are expected to implement multi-factor authentication and other security measures to protect against unauthorized access.
Compliance with these regulations often requires financial institutions to work closely with their SMS messaging service providers to ensure that the services they use meet the necessary security standards. This includes verifying that the provider’s infrastructure is secure, that messages are encrypted, and that data is handled in compliance with applicable laws.
Challenges in Securing Financial SMS
Securing financial SMS communications presents several challenges, primarily due to the inherent vulnerabilities of SMS as a communication channel. One of the main challenges is the lack of encryption in traditional SMS, which makes it susceptible to interception and unauthorized access.
Another challenge is balancing security with user experience. While implementing advanced security measures, such as multi-factor authentication and end-to-end encryption, is essential, it’s also important to ensure that these measures do not overly complicate the user experience. Customers expect quick and easy access to their financial information, and overly complex security protocols can lead to frustration and decreased satisfaction.
To overcome these challenges, financial institutions need to adopt a holistic approach to SMS security. This involves not only implementing robust security technologies but also designing user-friendly processes that make it easy for customers to engage with secure SMS communications.
The Future of Secure SMS in Finance
The future of secure SMS in finance is likely to be shaped by emerging technologies such as artificial intelligence (AI) and blockchain. AI has the potential to enhance SMS security by enabling more sophisticated fraud detection and response mechanisms. For example, AI algorithms can analyze patterns in SMS communications to identify unusual activity, such as repeated requests for OTPs, which may indicate a security breach.
Blockchain technology could also play a role in securing financial SMS. By using blockchain’s decentralized ledger to verify the authenticity of SMS messages, financial institutions can ensure that messages are tamper-proof and that the sender’s identity is verified.
As these technologies continue to evolve, financial institutions will need to stay ahead of the curve by integrating them into their SMS security strategies. This will not only enhance the security of financial SMS communications but also ensure that customers continue to trust SMS as a reliable and secure communication channel.
As financial services continue to evolve in the digital age, the need for secure SMS in financial SMS transactions has never been greater. With cyber threats on the rise, financial institutions must prioritize the security of their SMS communications to protect customer data and maintain trust. By implementing robust security measures, staying compliant with regulations, and embracing emerging technologies, financial institutions can ensure that their SMS communications remain secure and reliable.
The future of secure SMS in finance is promising, with advancements in AI and blockchain poised to further enhance security. Financial institutions that proactively invest in secure SMS solutions will not only safeguard their customers but also position themselves as leaders in the industry. As such, now is the time for financial institutions to prioritize secure SMS in their communication strategies and take the necessary steps to protect their customers and their business.
FAQs for Secure SMS in Financial Transactions
- What is secure SMS, and why is it important in financial transactions?
Secure SMS refers to SMS messages that are protected with encryption and other security measures to prevent unauthorized access. In financial transactions, secure SMS is crucial because it safeguards sensitive information like transaction alerts and one-time passwords (OTPs) from being intercepted by cybercriminals.
- How does encryption work in secure SMS?
Encryption in secure SMS converts the content of a message into a coded format that can only be deciphered by the intended recipient. This ensures that even if the message is intercepted, it cannot be read without the decryption key, protecting the privacy and integrity of the communication.
- What are common uses of financial SMS in banking?
Financial SMS is commonly used for sending transaction alerts, balance notifications, fraud detection warnings, and OTPs for two-factor authentication. These messages keep customers informed about their financial activities and add an extra layer of security to online transactions.
- What risks are associated with unsecured SMS in financial transactions?
Unsecured SMS can be intercepted by cybercriminals through methods like SIM swapping or man-in-the-middle attacks. If sensitive information like OTPs or transaction alerts is compromised, it can lead to unauthorized access to financial accounts and potential financial loss.
- How can financial institutions implement secure SMS?
Financial institutions can implement secure SMS by using end-to-end encryption, secure messaging gateways, and two-factor authentication. Regular security audits and educating customers on SMS security best practices are also essential for maintaining secure communications.
- What regulations govern financial SMS communications?
Financial SMS communications are subject to regulations like the General Data Protection Regulation (GDPR) in the EU and guidelines from the Federal Financial Institutions Examination Council (FFIEC) in the US. These regulations require financial institutions to implement security measures to protect customer data and ensure privacy.
- What are the challenges in securing financial SMS?
Challenges in securing financial SMS include the inherent vulnerabilities of traditional SMS, such as the lack of encryption, and the need to balance security with user experience. Financial institutions must adopt a holistic approach to address these challenges effectively.
- How might AI and blockchain impact the future of secure SMS in finance?
AI can enhance secure SMS by improving fraud detection and automating responses to suspicious activity. Blockchain technology could be used to verify the authenticity of SMS messages, ensuring they are tamper-proof and that the sender’s identity is verified.
- What are some examples of financial institutions successfully using secure SMS?
Examples include a global bank that reduced fraudulent transactions by partnering with a secure SMS provider offering end-to-end encryption, and a fintech company that used secure SMS gateways for delivering OTPs, achieving high security without compromising user experience.
Business Solutions
הטכנולוגיות שמשנות את שוק הבנייה הישראלי ב-2025 – ואיך להיות מוכן
מבוא
שוק הבנייה הישראלי עומד בפני שינוי מבני מואץ. לחצי עלות, מחסור בכוח אדם מיומן, עליות בחומרי גלם וגידול בביקוש לדיור – כל אלה מאלצים חברות בנייה לחפש יעילות מקומות שלא חיפשו קודם. הפתרון מגיע מהטכנולוגיה. בשנת 2025, חמש טכנולוגיות עומדות במרכז הטרנספורמציה הדיגיטלית של הענף – וחברות שמאמצות אותן מוקדם יותר יהנו מיתרון תחרותי משמעותי. ConWize היא דוגמה לפלטפורמה ישראלית שמשלבת כמה מהכלים הללו – אומדן, תמחור וניהול מכרזים – בפתרון אחד מאוחד, שנבנה על הצרכים הספציפיים של שוק הבנייה המקומי.
טכנולוגיה 1: BIM – מידול מידע לבניין
BIM (Building Information Modeling) אינה עוד חידוש – היא הופכת לסטנדרט עבודה. BIM מאפשרת יצירת מודל תלת-ממדי דיגיטלי של הבניין שכולל לא רק גיאומטריה אלא גם נתוני עלות, לוחות זמנים, מפרטים טכניים ותחזוקה עתידית.
אנגליה מחייבת BIM בכל מבנה ציבורי מ-2016
ישראל צפויה להרחיב דרישות BIM בפרויקטי תשתיות ממשלתיים ב-2025–2026
חיסכון ממוצע: 5–10% בעלויות בנייה, 20% בשגיאות תכנוני
טכנולוגיה 2: ניהול אומדן ותמחור בענן
גיליונות Excel אינם מספיקים יותר כשמנהלים מספר פרויקטים מורכבים בו-זמנית. פתרונות ענן לאומדן מאפשרים גישה בכל מקום, שיתוף פעולה בזמן אמת ועדכון מחירים אוטומטי. פלטפורמת ConWize לאומדן ותמחור מייצגת את הדור הבא של כלים אלה: ממשק עברי, כתב כמויות מובנה, ניהול מכרזים ושליטה בתקציב – הכל מקום אחד.
חיסכון ממוצע בזמן אומדן: 35–50%
ירידה בשגיאות תמחור: עד 70%
זמינות מהשטח: עדכון ומעקב ישירות מהסמארטפון
טכנולוגיה 3: פלטפורמות ניהול פרויקטים בענן
כלים כמו Procore, PlanGrid ומקבילות ישראליות מאפשרות ניהול לוחות זמנים, עבודות וחוזים מרכזי – עם ניראות מלאה לכל בעלי העניין בפרויקט. לפי Dodge Data & Analytics, חברות שמשתמשות בפלטפורמות ניהול פרויקטים מדווחות על עמידה בלוחות זמנים גבוהה ב-30% לעומת חברות שאינן משתמשות.
ניהול RFI ותוכניות ישירות מהאפליקציה
תיעוד אוטומטי של כל החלטה ואירוע בשטח
דשבורד סטטוס לכל קבלן ומשימה
טכנולוגיה 4: ניתוח נתוני שטח ו-IoT
חיישנים, מצלמות ומכשירי IoT שמוצבים באתר הבנייה מאפשרים מעקב בזמן אמת אחר התקדמות עבודות, שימוש בציוד ותנאי בטיחות. הנתונים מוזנים לפלטפורמות ניתוח שמאפשרות לזהות עיכובים, בזבוז ומפגעי בטיחות לפני שהם הופכים לבעיות.
ניטור ממשי של שעות עבודה ונוכחות
מעקב GPS אחר ציוד וכלי רכב
התראות בטיחות אוטומטיות
טכנולוגיה 5: בינה מלאכותית לתמחור ואומדן
הדור הבא של כלי האומדן משלב בינה מלאכותית שמנתחת פרויקטים קודמים ומחירי שוק כדי לייצר אומדנים מדויקים יותר. מערכות AI מסוגלות לזהות חריגות, להצביע על סיכוני עלות ולהציע חלופות תכנוניות זולות יותר – כל זאת בשבריר מהזמן שצוות אנושי היה זקוק לו.
לפי סקר Autodesk מ-2024, 68% ממנהלי הפרויקטים בעולם מאמינים ש-AI תהיה מרכזית בתמחור ואומדן תוך שלוש שנים.
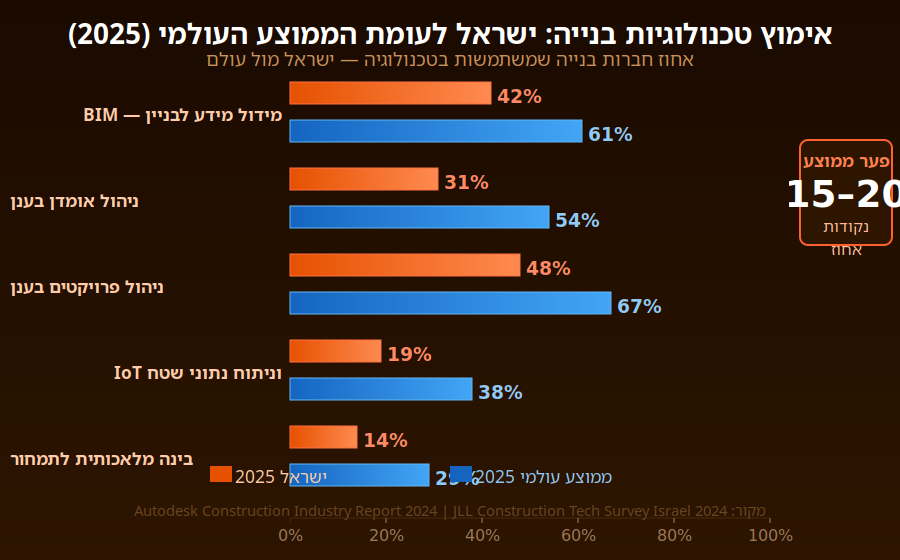
טבלת השוואה: שיעורי אימוץ טכנולוגיות בנייה בישראל (2025)
| טכנולוגיה | שיעור אימוץ (ישראל) | שיעור אימוץ (עולמי) |
| BIM | 42% | 61% |
| ניהול אומדן בענן | 31% | 54% |
| ניהול פרויקטים בענן | 48% | 67% |
| IoT וניתוח שטח | 19% | 38% |
| AI לתמחור ואומדן | 14% | 29% |
מקור: Autodesk Construction Industry Report 2024; JLL Construction Tech Survey Israel 2024
מה שוק הבנייה בישראלי צריך לדעת
ישראל מאמצת טכנולוגיות בנייה בקצב איטי יותר מהממוצע העולמי – אך הפער מצטמצם. הנהגת מחייבת BIM בפרויקטים ציבוריים, עלייה בהיקפי הבנייה ותחרות גוברת על כוח אדם מיומן יוצרים לחץ שמאיץ את קצב האימוץ. חברות שיתחילו את המעבר הדיגיטלי עכשיו ייהנו מיתרון ראשון-מגיע שיהיה קשה לשחזר בעוד שלוש שנים.
התחילו בכלי ה-ROI המהיר ביותר: ניהול אומדן ותמחור דיגיטלי
צרו מסד נתונים פנימי של עלויות מפרויקטים קודמים
השקיעו בהכשרת צוות – הטכנולוגיה טובה בדיוק כמו האנשים שמשתמשים בה
בחרו פלטפורמה עם תמיכה מקומית ותיעוד בעברית
סיכום
הטרנספורמציה הדיגיטלית של שוק הבנייה הישראלי אינה שאלה של ‘אם’ אלא של ‘מתי’. הכלים שפעם היו נחלת חברות הבנייה הגדולות ביותר בעולם הפכו נגישים, מותאמים מקומית ומוכחים בשטח. חברות שישכילו לאמץ טכנולוגיות אלה יוכלו לנהל פרויקטים מורכבים יותר, לשמור על שולי רווח בריאים ולספק ללקוחות שלהן רמת מקצועיות שהמתחרים לא יוכלו להציע. זהו הרגע לפעול
Business Solutions
Conwize: Quoting Software for Builders with Integrated Construction Bid Management
In competitive construction markets, how you quote is as important as what you quote. Builders and contractors that produce fast, accurate, professionally presented quotations – and that track their bidding activity systematically through a structured construction bid management software – consistently win more work at better margins than those who treat quoting as a reactive administrative task. Conwize is built on this insight, providing quoting software for builders that transforms pre-construction commercial operations from a pressure point into a competitive advantage.
The Commercial Cost of Inadequate Quoting Tools
The construction industry’s quoting and bidding function consumes a substantial proportion of a contracting business’s overhead – estimating teams, bid coordinators, quantity surveyors, and management time all contribute to the cost of pursuing work that may or may not be won. Industry benchmarks suggest that the estimating cost per bid ranges from 0.1% to 0.5% of project value for sophisticated estimating operations, and considerably more for businesses using manual, inefficient processes.
The opportunity cost of inadequate quoting software for builders is even larger. Teams hampered by slow, manual quoting processes cannot pursue as many tenders as the market makes available. Errors in manually assembled quotes – whether missed cost items, transposition errors, or outdated subcontractor prices — either cost margin when not caught before submission or cost the bid when detected by the client during evaluation. And the lack of systematic construction bid management means that business development intelligence – which project types are most winnable, which clients award most reliably, which geographies have the best margin potential – is never captured or analyzed.
Conwize addresses all three dimensions of this challenge: faster quoting through workflow automation, more accurate quotes through integrated subcontractor pricing, and richer bid intelligence through systematic pipeline management.
How Conwize’s Quoting Workflow Works for Builders
When a tender invitation arrives, Conwize’s quoting workflow begins with a single project setup action: the estimator creates a new project, loads the tender documents, and structures the scope into trade packages. From this point, the entire quoting process runs within Conwize – with no information escaping into external spreadsheets or email threads that cannot be tracked or controlled.
The subcontractor quotation process — typically the most time-consuming element of any builder’s quoting workflow – is where Conwize delivers its most immediate time savings. Scope packages are prepared within the platform and distributed to selected subcontractors in a single action. Subcontractors receive a structured invitation with all relevant documents attached. Response receipt is tracked automatically. Reminder notifications go out to non-responding subcontractors without manual chasing. And received quotations are loaded into Conwize’s bid comparison interface for structured analysis.
The bid comparison and leveling interface presents all received subcontractor quotations side by side against the scope items, automatically calculating adjusted totals that account for scope gaps, and flagging the most competitive compliant offer for each package. What takes a day or more of manual analysis in a spreadsheet is accomplished in Conwize in under an hour — with a complete, documented audit trail of the comparison.
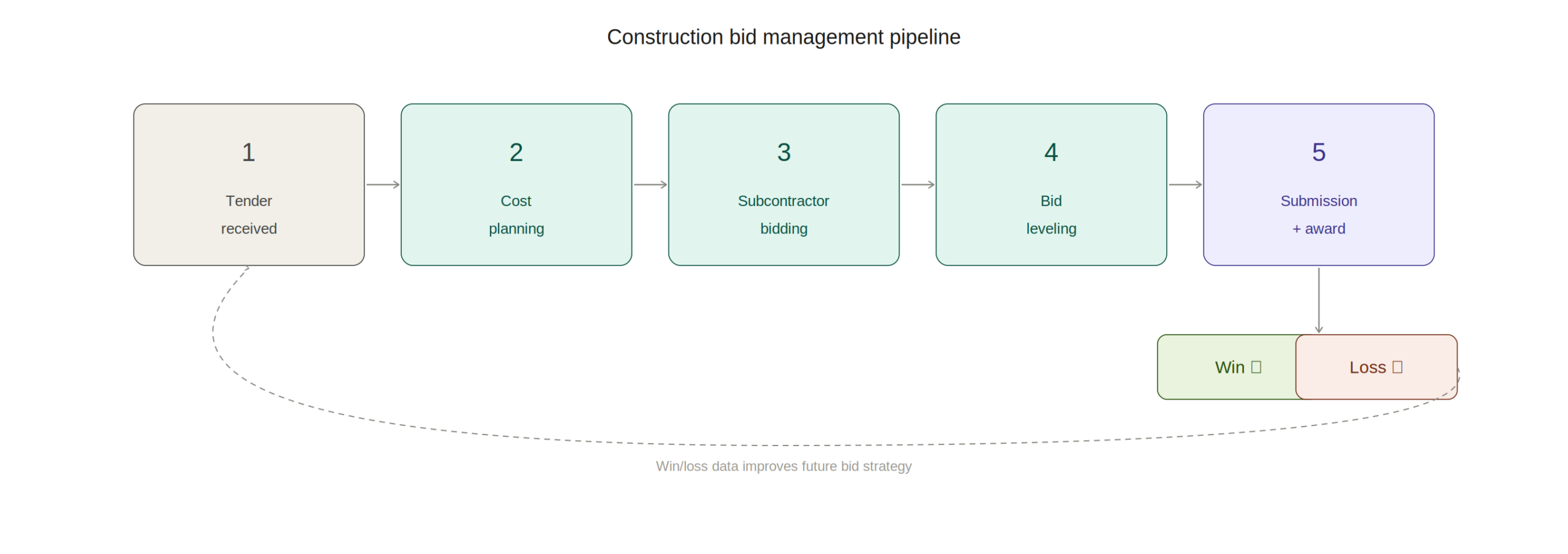
Construction Bid Management: The Strategic Layer Above Quoting
Quoting individual tenders is a tactical activity; construction bid management is the strategic framework that ensures the quoting function serves the business’s commercial objectives. Effective bid management means having a clear, systematically applied bid/no-bid decision process, a structured pipeline of active tenders with visibility of deadlines and resource requirements, and a rigorous post-submission win/loss analysis process that feeds continuous improvement of the bidding strategy.
Conwize’s bid management capability provides all three elements. The pipeline dashboard gives construction directors and business development managers a real-time view of every active tender – project value, client, submission deadline, responsible estimator, and current status. This visibility enables informed bid/no-bid decisions on new opportunities and supports resource allocation decisions that ensure the most commercially important bids receive appropriate attention.
For a detailed breakdown of how systematic construction bid management transforms pre-construction commercial operations, Conwize’s dedicated article on construction bid management covers the key components — from pipeline design to win/loss analysis frameworks — in detail. The discipline of managing bids systematically rather than reactively is one of the most significant changes a construction business can make to its commercial performance.
Subcontractor Management Within the Quoting Platform
The quality of a builder’s subcontractor network is a direct determinant of the quality of their quotations – and managing that network effectively requires more than a contacts list. Conwize’s subcontractor database tracks each subcontractor’s trade coverage, geographic range, response rate, historical pricing competitiveness, and performance on awarded projects — providing the intelligence needed to assemble the best tender list for each trade package on each new project.
Over time, this intelligence compounds: estimators can see which subcontractors consistently respond with competitive prices for specific trade types, which tend to submit incomplete scope, and which have the highest award rates. This data-driven tender list selection is a significant quality improvement over the informal, relationship-based subcontractor selection that most builders currently practice.
The Conwize subcontractor portal – through which subcontractors receive invitations, submit quotations, and track their own bid history – is designed for ease of use from the subcontractor’s perspective, increasing response rates and improving the quality of received quotations.
Frequently Asked Questions
Q1: What is quoting software for builders and how does it differ from generic estimating tools?
A: Quoting software for builders is specifically designed for the construction quoting workflow – managing the complete process from scope definition through subcontractor bid management to submission document generation. Generic estimating tools focus on cost calculation; purpose-built quoting software manages the entire commercial workflow surrounding that calculation.
Q2: What is construction bid management and why is it important?
A: Construction bid management is the systematic process of tracking, coordinating, and analyzing the full bidding lifecycle – from tender identification and bid/no-bid decision through to submission, award, and win/loss review. Systematic bid management transforms bidding from a reactive activity into a managed commercial function with measurable performance improvement over time.
Q3: How does Conwize’s quoting workflow save time for builders?
A: Conwize automates the most time-consuming elements: subcontractor invitation and tracking (replacing manual email management), bid leveling (replacing manual spreadsheet comparison), and submission document generation (replacing manual reformatting). These automations typically reduce quoting time by 30-50% per tender.
Q4: Can Conwize track multiple simultaneous tenders in the bid pipeline?
A: Yes. Conwize’s pipeline dashboard displays all active tenders – value, deadline, client, status, and responsible estimator – in a single management view. This enables directors to allocate estimating resources, make bid/no-bid decisions, and track portfolio-level bidding activity in real time.
Q5: How does Conwize support post-bid win/loss analysis?
A: Conwize records bid outcomes — win/loss status, awarded value, client, project type, and geographic location – enabling systematic analysis of win rates by project type, client sector, tender value range, and other dimensions. This intelligence informs continuous improvement of bidding strategy and target market selection.
Q6: Does Conwize help with subcontractor response rates on quotation requests?
A: Yes. Conwize sends automated follow-up reminders to subcontractors who have not responded to quotation invitations, significantly improving response rates without manual chasing. The subcontractor portal provides a simple, accessible submission interface that further encourages response.
Q7: Is Conwize suitable for both residential builders and commercial contractors?
A: Conwize serves both residential builders managing volume quoting workflows and commercial contractors pursuing complex multi-trade tenders. The platform scales from straightforward residential quotations to sophisticated commercial BOQ-based estimates with comprehensive subcontractor bid management.
Business Solutions
Conwize for Building Costing and Construction Budgeting: Platform Overview and Key Capabilities
At a Glance
- Building costing is the financial foundation of every construction project – establishing the cost baseline against which all scope changes, subcontractor prices, and project decisions are measured from concept through to completion.
- Construction budgeting software has evolved from static spreadsheet tools into dynamic platforms that connect cost plans to live market pricing, subcontractor quotations, and real-time cost reporting — delivering the cost intelligence that drives profitable project delivery.
- Conwize serves general contractors, head contractors, and specialty contractors who need accurate, auditable building cost plans that can be produced efficiently, reviewed collaboratively, and updated automatically as pricing and scope evolve.
- Conwize’s competitive advantage is the integration of building costing, subcontractor bid management, and tender pipeline tracking in a single cloud-native platform – eliminating the disconnected tools and manual processes that inflate estimating overhead and introduce commercial risk.
The financial outcome of a construction project is largely determined before construction begins – by the quality of the building costing process that establishes the project budget and the rigor of the construction budgeting software that supports it. Conwize was designed by people who understand this reality: that accurate, efficient, and continuously updated cost plans are not just an estimating deliverable but the commercial architecture that underpins every profitable project.
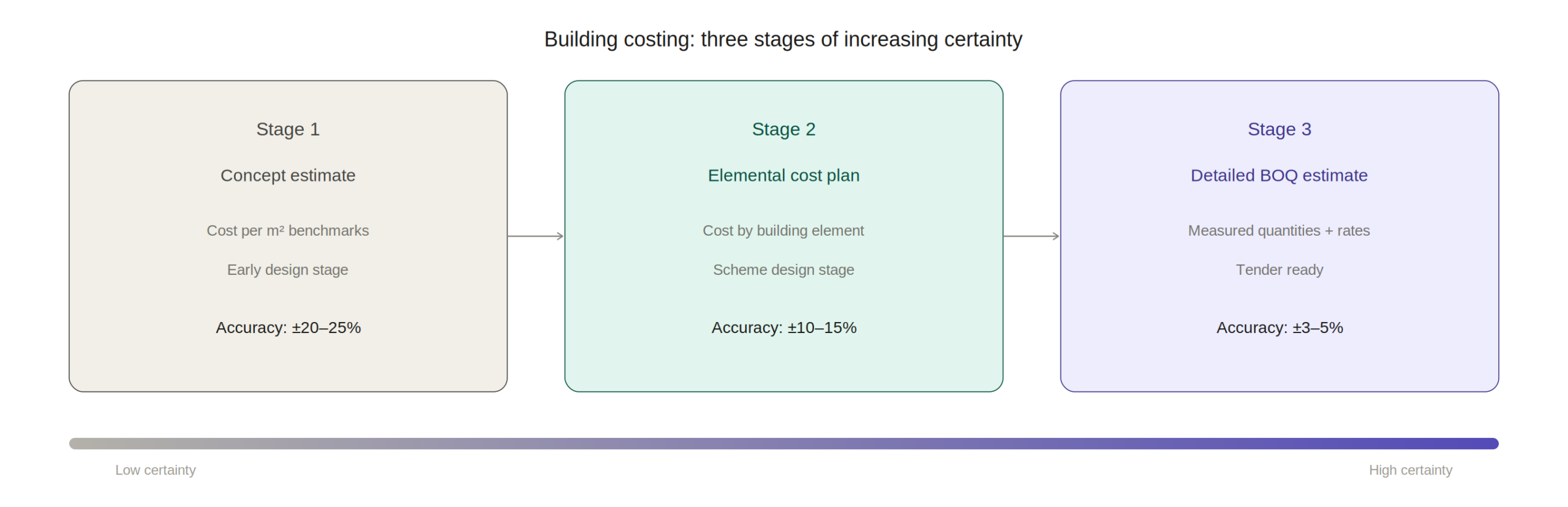
Building Costing: The Foundation of Project Commercial Management
Building costing encompasses the complete process of estimating and managing the cost of constructing a built asset – from the initial elemental cost plan produced at concept design stage through to the detailed BOQ-based budget prepared for tender, and the live cost reporting that tracks actual versus budget throughout delivery. Each stage has different information requirements, different levels of certainty, and different commercial implications.
At the concept stage, building costing relies on parametric benchmarks – cost per square meter by building type, elemental cost ratios, and market intelligence about prevailing construction costs in the relevant geography. At the scheme design stage, an elemental cost plan breaks the building cost into functional elements (substructure, superstructure, envelope, fit-out) with budgets for each based on more developed design information. At the tender stage, the detailed building costing exercise produces a priced BOQ based on measured quantities and actual subcontractor and supplier prices.
Conwize supports all three stages within a single platform – allowing the cost plan to evolve from parametric concept estimate through to detailed tender cost without losing data continuity. The concept stage assumptions are retained as audit trail as the estimate develops, providing a clear picture of how cost certainty has improved through the design process. For a comprehensive guide to building costing methodology, Conwize’s dedicated resource at the Estimating Building Costing guide covers each stage in detail.
Why Traditional Construction Budgeting Software Falls Short
The most common construction budgeting software tool in the industry is still the spreadsheet — and its limitations are well understood. Spreadsheet cost plans break under collaborative use, with version control chaos when multiple team members need to update the same document. They lack integration with live pricing, requiring manual re-entry of subcontractor quotations. They provide no portfolio-level visibility into multiple simultaneous estimates. And they produce no automatic reporting, requiring manual extraction and reformatting of cost data for every client or management report.
Legacy desktop estimating tools solve some of these problems but introduce others. They provide more structure than spreadsheets and typically include cost database functionality, but their desktop architecture prevents genuine multi-user collaboration and remote access. Updates require manual installation, and data backup depends on individual users’ practices rather than automatic cloud sync.
Cloud-native construction budgeting software like Conwize addresses all of these limitations simultaneously. Real-time collaboration, automatic cloud backup, live pricing integration, and portfolio-level reporting are all native capabilities – not bolt-on features. This architectural advantage is the fundamental reason cloud platforms are displacing legacy tools as the standard for professional construction estimating operations.
Conwize’s Building Costing Workflow
Conwize structures building costing within a consistent, project-level cost breakdown that mirrors the actual trade package structure of construction projects. Estimators work within a defined hierarchy – from high-level elemental groups down to individual trade packages and line-item cost components — providing both the structure needed for management-level reporting and the detail needed for subcontractor procurement.
The platform’s assembly library enables estimators to build trade package budgets from pre-configured assemblies of labor, material, and plant components – applying regional rate adjustments and project-specific escalations to produce location-calibrated estimates. For projects where a client-provided BOQ is available, Conwize supports direct import of BOQ items, allowing the cost plan to be structured around the client’s measurement framework rather than an internally developed structure.
Subcontractor pricing integration is where Conwize’s building costing capability differentiates most significantly from spreadsheet and legacy alternatives. Estimators can issue RFQ packages directly from cost plan line items, receive quotations back into the platform, and automatically update the relevant budget items with received prices – replacing the manual data re-entry that introduces errors and delays in spreadsheet-based workflows. The live budget position updates in real time as pricing is received, giving management a continuously current view of cost plan status.
Real-Time Cost Reporting and Budget Tracking
The most valuable aspect of Conwize as construction budgeting software is the live reporting capability that transforms cost planning from a periodic exercise into a continuous operational intelligence function. Project directors can access the current cost plan status at any time – seeing which packages have been priced, which subcontractor quotations are outstanding, what the projected final cost looks like against the budget, and where cost risk is concentrated.
This live visibility is particularly valuable in fast-moving tender environments where subcontractor pricing is arriving right up to submission deadline. Rather than scrambling to update a spreadsheet cost plan manually with last-minute prices and hoping the totals are correct, Conwize users have a live cost total that updates automatically as each quotation is received – enabling confident bid submission even when pricing arrives late.
Conwize’s reporting layer generates client-ready cost plan documents, internal management summaries, and audit-trail reports directly from the platform’s live cost data – eliminating the manual reformatting step that typically consumes 10-15% of estimating team time in manual cost planning processes. Explore the full platform capability for general contractors at conwize.io, and for expert analysis of how digital tools are transforming construction cost management, techpr.online provides regular coverage of construction technology innovation.
Managing Cost Risk and Contingency in Building Projects
Every building cost plan carries uncertainty – from design incompleteness at early stages to market pricing volatility throughout the project duration. Professional building costing practice requires systematic identification and quantification of this uncertainty, and Conwize supports formal cost risk management within the estimating workflow.
Estimators can apply percentage-based or absolute contingency provisions at any level of the cost breakdown – from individual line items through to trade package totals and overall project budget. High-uncertainty items can be flagged for management attention, and sensitivity analysis scenarios can be modeled to show how the budget changes under different pricing assumptions.
Over time, Conwize’s historical data accumulation enables increasingly sophisticated risk management: as actual subcontractor prices from completed projects are retained in the platform, estimators can benchmark current estimates against empirical historical data, identifying systematic biases in their pricing assumptions and calibrating contingency provisions with greater confidence.
Frequently Asked Questions
Q1: What is building costing and how does it differ from construction estimating?
A: Building costing refers broadly to the process of establishing and managing a project’s cost – from early parametric cost plans at concept design through to detailed tender estimates. Construction estimating typically refers specifically to the detailed cost build-up produced for tender submission. Both functions are supported within Conwize’s single integrated platform.
Q2: What makes Conwize different from spreadsheet-based construction budgeting software?
A: Conwize provides real-time multi-user collaboration, live subcontractor pricing integration, automatic reporting, and portfolio-level pipeline visibility – capabilities that spreadsheets architecturally cannot deliver. It also maintains data continuity from concept estimate through to subcontract award, eliminating the version-control and data re-entry problems that spreadsheet workflows produce.
Q3: Can Conwize handle both elemental cost planning and detailed BOQ estimating?
A: Yes. Conwize supports parametric and elemental cost planning at early design stages, and detailed BOQ-level estimating for tender submission – within the same project, maintaining data continuity as the estimate develops from concept through to detailed submission.
Q4: How does Conwize integrate subcontractor pricing into the building cost plan?
A: Conwize allows estimators to issue RFQ packages directly from cost plan items and receive quotations back into the platform. Received prices automatically update the relevant budget items, and the live cost total reflects the current pricing position in real time – no manual re-entry required.
Q5: What cost risk management features does Conwize provide?
A: Conwize supports percentage-based and absolute contingency provisions at any level of the cost breakdown, sensitivity scenario modeling, and flagging of high-uncertainty items. Historical cost comparison against completed projects further informs contingency calibration.
Q6: How does Conwize’s reporting capability work for building cost plans?
A: Conwize generates client-ready cost plan documents, management summaries, and audit-trail reports directly from the live cost data – eliminating manual reformatting. Reports update automatically as new pricing is received or scope changes are incorporated.
Q7: Is Conwize suitable for contractors who receive client-provided BOQs to price?
A: Yes. Conwize supports import of client-provided BOQs in CSV and Excel formats, allowing estimators to work within the client’s measurement framework rather than rebuilding the cost structure from scratch. Subcontractor prices can be linked directly to imported BOQ items.
-

 Business Solutions2 years ago
Business Solutions2 years agoLive Video Broadcasting with Bonded Transmission Technology
-

 Business Solutions1 year ago
Business Solutions1 year agoThe Future of Healthcare SMS and RCS Messaging
-

 Business Solutions2 years ago
Business Solutions2 years ago2-Way Texting Solutions from Company Message Services
-

 Business Solutions2 years ago
Business Solutions2 years agoCommunication with Analog to Fiber Converters & RF Link Budgets
-

 DSRC Communication1 year ago
DSRC Communication1 year agoThe Crossroads of Connectivity: DSRC vs. C-V2X Technologies in Automotive Communication
-
Electronics3 years ago
AI Modules and Smart Home Chips: Future of Home Automation
-

 Business Solutions2 years ago
Business Solutions2 years agoWholesale SMS Platforms with OTP Services
-
 Business Solutions2 years ago
Business Solutions2 years agoAerial Wind Turbine Inspection with Advanced Camera Drones




