Cybersecurity
A Guide to Threat Intelligence on the Web
In the modern cybersecurity world, collecting threat intelligence is crucial for the security of organizations. It’s not enough to use the right security tools and adopt cybersecurity best practices. It’s not enough to educate employees on issues such as phishing.
In addition to the above, it has become necessary to leave the safety of your domain and venture outwards to gather intelligence, sometimes into enemy territory.
Gathering actionable threat intelligence on the web is no mean feat. There is a lot of unstructured data. Every step in the process, from data collection to structuring to processing to advanced analysis is complex.
However, thanks to machine learning and artificial intelligence, threat intelligence on the web is not only a feasible endeavor but also a beneficial one.
Additionally, thanks to a range of tools, along with OSINT techniques, valuable data can be extracted from the web.
The OSINT Methodology
OSINT is an acronym that stands for Open Source Intelligence. This is threat intelligence collected from various sources of data on the internet. It is called open source because it uses data that is publicly and legally accessible.
Sources of OSINT include blogs, the comments sections of websites, online forums, online directories and databases, and online tools such as reverse image and image metadata tools.
OSINT techniques involve accessing information from these sources and processing it to generate actionable threat intelligence.
OSINT and the Dark Web
The dark web is significantly less accessible compared to the open web. Most of the websites there are not indexed. Furthermore, websites on the dark web can’t be accessed with normal browsers. They need special tor browsers.
Because of the barriers to access listed above, in addition to others, the dark web is out of reach for many people.
Still, it is a source of valuable information. In fact, with regards to cybersecurity, information obtained from the dark web can be several times more valuable than information obtained from the open web. This is because threat actors are generally more active on the dark web.
Proper threat intelligence collected over the web has to include sources from the dark web.
What is Dark Web Threat Intelligence?
Threat intelligence on the dark web is the collection of data from various websites and forums on the dark web to generate insights on potential cyber attacks and improve cyber security for organizations.
The dark web is a hub for cybercrime in more than one way:
- It facilitates communication and collaboration among threat actors
- It enables the exchange of advanced cybercrime tools such as state-of-the-art malware
- It facilitates the sale and purchase of data acquired from successful breaches. Such data, if purchased by threat actors, can be used to engineer further attacks against organizations.
- When used together with modern means of payment such as cryptocurrency, which are significantly less traceable than conventional means, it enables illegal transactions to be conducted in ample privacy.
Given how the dark web facilitates cybercrime, conducting threat intelligence on the dark web is an effective technique in cyber security. It can help improve the general security profile of an organization and even help thwart attacks.
How Threat Intelligence on the Dark Web Helps Organizations Boost Cybersecurity
Collecting threat data from the dark web isn’t easy. Analyzing and making sense of it is even more difficult. There are significant security considerations to make when venturing into the dark web. In addition, accessibility isn’t easy because joining most forums requires establishing trust with criminals.
However, braving these challenges is worth it. Here’s how companies benefit from dark web threat intelligence:
- If there’s been a security breach and your data is put up for sale on the dark web, you could buy it back. This ensures that it doesn’t fall into the hands of threat actors who would use it to perpetuate more damage against your organization.
- It can be a useful source of information on threat actors. Analyzing data from multiple platforms on the dark web could provide useful insights into the techniques and motivations of pertinent threat actors, making your organization more prepared and more secure.
- It helps generate real-time alerts, which can help thwart attacks. With the help of advanced artificial intelligence software, which are capable of analyzing the big data of the dark web as it is generated, your company could get real-time alerts when events of interest occur. For example, you could get notified the moment your name appears on a dark web forum.
- Investigating threat actors becomes easier. Most cybercriminals conduct most of their online activity on the dark web. Having access to dark web data can help shed light on the identities, locations, and actions of threat actors. Such information can help stop them.
- It can help with evidence for prosecution. Analyzing multiple sources on the dark web could reveal evidence that could be used to prosecute threat actors.
- It helps identify breaches and address them. If you find your organization’s data on the dark web, you can perform an audit to find out how the breach occurred. Sometimes, if you are not monitoring the dark web, it can take longer to identify a data breach and correct it. This can lead to more attacks.
Conclusion
The modern cybersecurity landscape necessitates the collection of web intelligence. Though web intelligence is not easy, it comes with significant benefits. It can help organizations adopt a more proactive approach to cybersecurity, one which helps stop some attacks before they happen.
Open source intelligence, including that from the dark web, is crucial in the collection of threat intelligence on the web.
Cybersecurity
Microsoft Power Platform Security: The Risks You Cannot See and How to Address Them
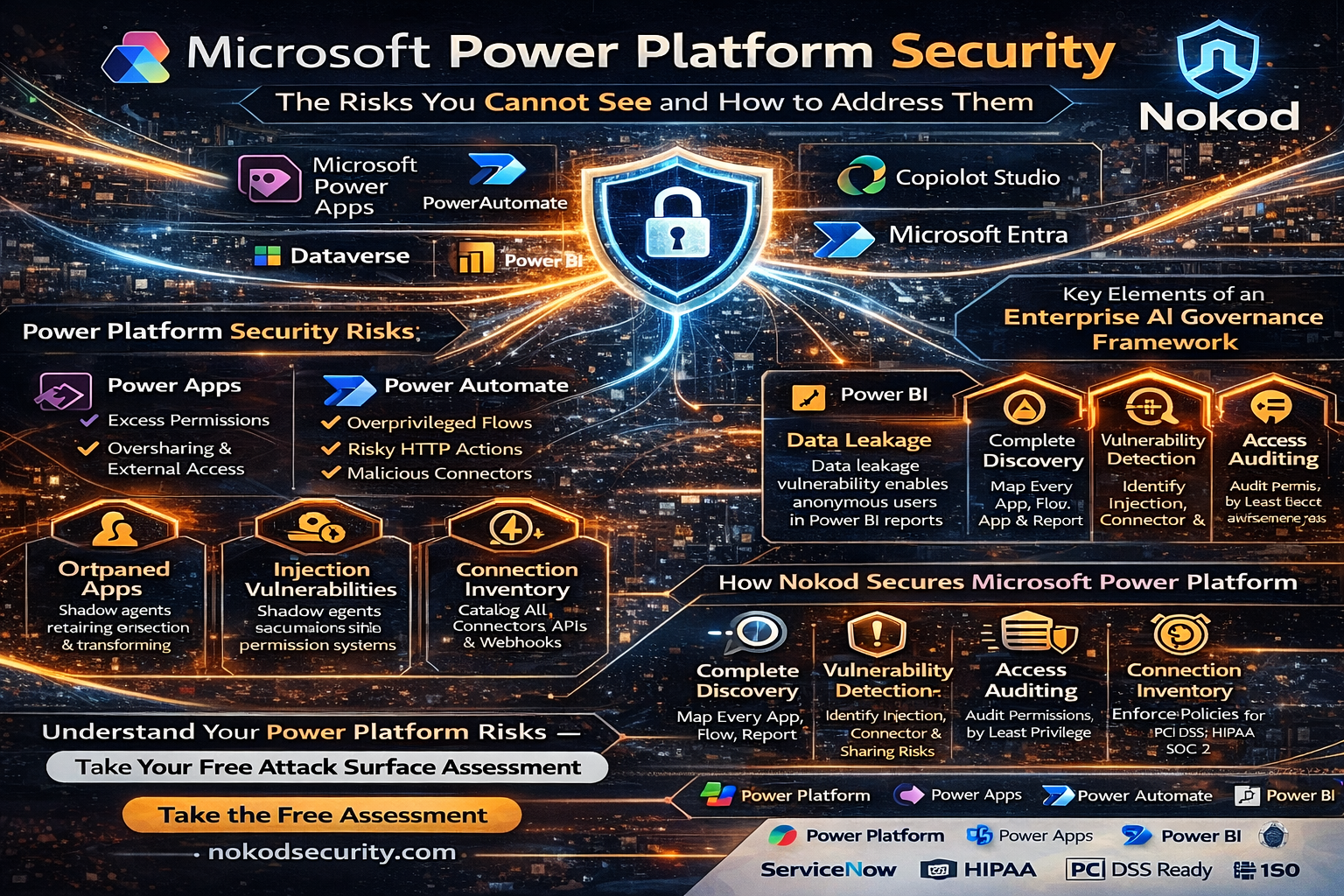
Microsoft Power Platform has become the backbone of citizen development across enterprises worldwide. Power Apps, Power Automate, Power BI, and Copilot Studio collectively enable millions of business users to build applications, automate workflows, analyze data, and deploy AI agents – all without writing code. But the same capabilities that make Power Platform indispensable also make it one of the most significant unmanaged security risks in the modern enterprise. This article examines the security challenges specific to Microsoft Power Platform and explains how Nokod Security addresses them.
Why Microsoft Power Platform Creates a New Security Paradigm
Power Platform is not a single product. It is an integrated ecosystem of tools that share a common data platform (Dataverse), a common connector framework, and a common identity model (Microsoft Entra). When a citizen developer builds a Power App that calls a Power Automate flow that reads from SharePoint and writes to SQL Server, they are creating a multi-system data pathway that traditional AppSec tools are entirely blind to.
The challenge is amplified by scale. According to Nokod, the average enterprise contains more than 10,000 business-built apps. A significant proportion of these are Power Platform applications and flows. Twenty percent of no-code apps are exposed externally. The gap between what security teams think they have and what exists in reality is one hundred percent.
Power Platform Security Risks: What Security Teams Need to Understand
The security risks within Microsoft Power Platform span all three major components:
Power Apps
- Apps built with excess permissions that allow access to sensitive Dataverse tables beyond what users need
- Apps shared tenant-wide or externally, making internal data accessible to unauthorized users
- Orphaned apps retaining connections and permissions after their creator has left the organization
- Injection vulnerabilities embedded in app logic that processes user input
Power Automate
- Flows that run under service accounts with overprivileged access to critical systems
- Unencrypted HTTP actions sending sensitive data to external endpoints
- Malicious third-party connectors embedded in automation workflows
- Flows triggering unauthorized actions in downstream systems like ERPs and CRMs
Power BI
The Nokod Research Team discovered a significant data leakage vulnerability in the Microsoft Power BI service affecting potentially tens of thousands of organizations. The issue relates to the relationship between Power BI report objects and their underlying semantic models. When a Power BI report is shared with users, all raw data represented by the underlying semantic model is also accessible to those users – including detailed data records that are used only for aggregations in the report UI. This means anonymous viewers may be able to access sensitive data, including employee data, business data, PHI, and PII, even when the report is not intended to surface that information.
Nokod reported the finding to the Microsoft Security Response Center (MSRC) and created a free Power BI Analyzer tool to help organizations assess their exposure to this vulnerability.
How Nokod Secures Microsoft Power Platform
Nokod Security offers a free attack surface assessment tool for Microsoft Power Platform, allowing organizations to immediately understand the scope of their exposure before committing to a full deployment. The full Nokod platform integrates with the Power Platform environment within minutes, using the native API to deliver comprehensive visibility across all apps, flows, and connected services.
Key capabilities for Power Platform security include:
- Complete discovery of all Power Apps, Power Automate flows, and Power BI reports across the tenant
- Inventory of all connections and connectors, including third-party and custom connectors
- Vulnerability detection for injection attacks, insecure HTTP calls, risky webhooks, and malicious integrations
- Access and permission auditing, including identification of excess permissions and oversharing
- Governance policy management with automated remediation and developer-friendly guidance
- Compliance monitoring for regulatory requirements including PCI DSS, HIPAA, and SOC 2
Power Platform Security and the Broader Enterprise LCNC Landscape
Power Platform rarely exists in isolation within an enterprise. It connects to SharePoint, Teams, Dataverse, Azure services, Salesforce, ServiceNow, and dozens of third-party systems. Security governance that addresses only Power Platform leaves significant gaps.
Nokod’s approach is inherently multi-platform. By providing a single security and governance layer across all citizen-developed and AI-agent-built applications – regardless of the underlying platform — Nokod enables security teams to see the full attack surface and apply consistent policies across every environment.
Nokod is ISO-certified and SOC 2 compliant, and its management team includes founders of Imperva and SecuredTouch (now Ping Identity), bringing decades of application security expertise to the LCNC and AI-agent security space.
To get started with Power Platform security, visit Nokod Power Platform Security. For information on securing Copilot Studio within your Power Platform environment, see Nokod Copilot Studio Security. To explore the full platform, visit nokodsecurity.com.
Frequently Asked Questions
Q: What is Microsoft Power Platform?
A: Microsoft Power Platform is an integrated suite of low-code tools including Power Apps, Power Automate, Power BI, and Copilot Studio. It enables business users to build applications, automate workflows, analyze data, and deploy AI agents without professional development skills.
Q: What Power BI vulnerability did Nokod discover?
A: The Nokod Research Team found that sharing a Power BI report also exposes all underlying raw data in the semantic model — including data not shown in the report UI- to all users with access. This can include sensitive PII, PHI, and business data.
Q: Does Nokod offer a free assessment for Power Platform?
A: Yes. Nokod Security provides a free attack surface assessment tool for Microsoft Power Platform to help organizations quickly understand their exposure.
Q: How does Nokod integrate with Power Platform?
A: Nokod connects to Power Platform through its native API and can deliver visibility within minutes of connection, without requiring any agents or endpoint installations.
Q: What compliance standards does Nokod support for Power Platform?
A: Nokod helps organizations achieve compliance with PCI DSS, HIPAA, SOC 2, and other regulatory frameworks within their Power Platform environments. Nokod itself is ISO-certified and SOC 2 compliant.
Business Solutions
Automotive IDS (Intrusion Detection Software): Safeguarding the Future of Connected Vehicles

The evolution of connected vehicles, autonomous driving systems, and over-the-air (OTA) updates has transformed the automotive industry into a high-tech environment. While these advancements offer numerous benefits, they also introduce new cybersecurity vulnerabilities. As modern vehicles become more complex and interconnected, the need to protect them from cyber-attacks becomes ever more urgent. One of the critical solutions to address these threats is the integration of Automotive Intrusion Detection Software (IDS Automotive).
Automotive IDS is designed to monitor vehicle systems in real-time, detect malicious activities, and respond to potential cybersecurity threats. In an era where vehicles are increasingly targeted by cybercriminals, an effective IDS plays a pivotal role in safeguarding not just the vehicle’s software and hardware, but also the safety of drivers, passengers, and other road users.
What is Automotive Intrusion Detection Software (IDS)?
Intrusion Detection Software (IDS) is a security technology that monitors and analyzes the activities of a system to detect signs of unauthorized access or suspicious behavior. In the context of automotive cybersecurity, IDS focuses on identifying and preventing attacks on a vehicle’s electronic control units (ECUs), communication networks, and other critical systems.
An automotive IDS typically operates by detecting irregularities in vehicle behavior that could indicate a cyberattack, such as unusual data traffic, unauthorized commands, or abnormal sensor readings. It analyzes the vehicle’s internal network traffic, such as Controller Area Network (CAN) bus, Ethernet, and FlexRay protocols, for any signs of intrusion or tampering.
How Automotive IDS Works
Automotive IDS operates in much the same way as traditional intrusion detection systems used in IT security, with some key differences specific to the automotive context:
1. Data Monitoring:
Automotive IDS continuously monitors the internal communication networks of a vehicle, including the CAN bus, Ethernet, and other communication channels. These networks serve as the backbone for data transmission between the vehicle’s various ECUs (e.g., engine control, infotainment, braking, steering), sensors, and actuators.
2. Anomaly Detection:
IDS systems typically use anomaly-based detection techniques to identify abnormal behavior in vehicle communication patterns. By establishing a baseline for “normal” vehicle behavior, the IDS can flag any activity that deviates from this baseline. Examples of anomalies could include unexpected changes in sensor readings, unusual messages between ECUs, or abnormal network traffic patterns that may indicate a cyberattack.
3. Signature-Based Detection:
Some IDS systems also use signature-based detection, which compares vehicle behavior against known attack signatures or pre-defined patterns of malicious activity. These signatures are updated regularly to reflect emerging threats, ensuring that the IDS can detect even the most recent attack methods.
4. Response Mechanisms:
Upon detecting a potential intrusion or anomaly, the IDS can trigger predefined responses to mitigate the threat. This may involve logging the event for further investigation, sending alerts to the vehicle’s central control unit, or taking immediate action such as isolating affected ECUs or triggering a failsafe mode to ensure safety.
5. Integration with Vehicle Security Systems:
An automotive IDS is typically integrated with other vehicle security systems, such as firewalls, secure communication protocols, and encryption mechanisms. This multi-layered security approach enhances the vehicle’s ability to prevent, detect, and respond to cyber threats.

Why is Automotive IDS Important?
The importance of Automotive IDS cannot be overstated in today’s connected car ecosystem. The integration of increasingly sophisticated technologies, like Advanced Driver Assistance Systems (ADAS) and autonomous driving features, has expanded the attack surface for potential cybercriminals. Here are several reasons why Automotive IDS is crucial:
1. Protecting Critical Vehicle Functions:
Modern vehicles are highly dependent on complex electronic systems to manage safety-critical functions, such as braking, steering, and acceleration. A successful cyberattack on these systems could have catastrophic consequences. Automotive IDS helps prevent unauthorized access to these systems by detecting and responding to potential threats in real-time.
2. Early Detection of Cyber Threats:
Intrusion detection software is one of the best tools for identifying cyberattacks before they can do significant damage. Whether it’s a remote hacker attempting to gain control of a vehicle’s systems or a local attacker trying to exploit vulnerabilities, an IDS can alert the vehicle’s control systems to the presence of an attack, enabling timely countermeasures.
3. Mitigating Risks to Privacy:
Connected vehicles gather and share vast amounts of data, from GPS locations to personal preferences. Cybercriminals may target these data streams to compromise users’ privacy. Automotive IDS helps prevent data breaches by identifying suspicious activity on the vehicle’s communication channels.
4. Real-Time Monitoring and Response:
In contrast to traditional vehicle security solutions, which may only provide post-event analysis, IDS operates in real-time. This means that a vehicle’s security systems can immediately detect and respond to an ongoing attack, minimizing the potential damage and ensuring that the vehicle remains operational and safe.
5. Compliance with Regulatory Standards:
The automotive industry is subject to increasing regulatory scrutiny related to cybersecurity, including standards like ISO/SAE 21434 for automotive cybersecurity and the UN R155 regulation for vehicle cyber resilience. Implementing Automotive IDS can help manufacturers meet these regulatory requirements and demonstrate their commitment to vehicle safety and security.
Types of Automotive IDS
There are two main types of IDS that can be used in automotive cybersecurity:
1. Host-Based IDS (HIDS):
Host-based IDS operates on individual ECUs or control units within the vehicle. These systems monitor the specific behaviors of the vehicle’s hardware and software to detect intrusions. HIDS can track file integrity, system configurations, and application behavior, providing detailed insights into any changes that could indicate an attack.
2. Network-Based IDS (NIDS):
Network-based IDS monitors the vehicle’s communication networks, such as CAN and Ethernet, to detect unauthorized or suspicious network traffic. NIDS analyzes the flow of messages between ECUs, sensors, and other vehicle components, looking for signs of malicious activity or abnormal data exchanges.
In many cases, an automotive cybersecurity system will use a combination of both HIDS and NIDS to provide comprehensive coverage against cyber threats.
Challenges in Implementing Automotive IDS
While the benefits of automotive IDS are clear, the implementation of these systems comes with its own set of challenges:
1. Complex Vehicle Architectures:
Modern vehicles contain a vast array of ECUs, sensors, and communication networks, each with unique security needs. Designing an IDS system that can effectively monitor and protect all these components is complex and requires integration with the vehicle’s entire electronic ecosystem.
2. Real-Time Processing:
Given the critical nature of vehicle operations, IDS systems must be able to detect threats in real-time without causing delays or performance degradation. This requires high processing power and advanced algorithms capable of handling large amounts of data quickly and efficiently.
3. False Positives:
One of the challenges with any IDS system is minimizing false positives — situations where benign activity is mistakenly flagged as malicious. In automotive contexts, false positives can be particularly problematic, as they may cause unnecessary disruptions to vehicle operations or trigger incorrect safety measures.
4. Evolving Cyber Threats:
The cybersecurity landscape is constantly evolving, with new attack methods and vulnerabilities emerging regularly. Automotive IDS systems need to be updated continuously to stay ahead of these threats. This can require ongoing development and support to ensure that vehicles remain secure over time.
As the automotive industry embraces the future of connectivity and automation, the need for robust cybersecurity measures has never been more critical. Automotive Intrusion Detection Software (IDS) serves as a vital component in safeguarding vehicles from the growing threat of cyber-attacks. By detecting and mitigating potential intrusions in real-time, IDS helps protect not only vehicle safety and privacy but also the reputation of manufacturers in an increasingly security-conscious market. As automotive technology continues to advance, the role of IDS in ensuring the integrity of connected and autonomous vehicles will only become more important.
Cybersecurity
Israeli Cybersecurity Investments: Fueling Innovation and Growth
As cyber threats continue to increase in frequency and complexity, the need for robust cybersecurity measures has become more pertinent than ever. To combat these threats, companies worldwide are investing heavily in cybersecurity technologies and services. In recent years, Israel has emerged as a leading hub for cybersecurity innovation and expertise, attracting significant venture capital investments in the sector. In this blog post, we will explore how cybersecurity venture capital investments are fueling innovation and growth in Israel’s cybersecurity industry, and why this trend is likely to continue in the years ahead. We will also examine some of the most promising Israeli cybersecurity startups that have attracted significant investments and are poised to make a significant impact in the global cybersecurity market.

Israel has emerged as a global hub for cybersecurity, attracting significant investments and establishing itself as a leader in the field. The country’s thriving cybersecurity ecosystem is supported by a robust network of early-stage venture capital (VC) firms that fuel innovation and drive the growth of cybersecurity startups. In this article, we will explore the landscape of Israeli cybersecurity investments and the role played by early-stage venture capital.
Israel’s Reputation as a Cybersecurity Powerhouse
Israel has gained a well-deserved reputation as a cybersecurity powerhouse, known for its cutting-edge technologies and expertise. This reputation is bolstered by a combination of factors, including a strong focus on cybersecurity education, close collaboration between the military and the private sector, and a culture of innovation and entrepreneurship.
The Role of Early-Stage Venture Capital (VC) in Israel
Early-stage venture capital firms play a vital role in the Israeli cybersecurity ecosystem. These firms provide crucial funding, guidance, and support to cybersecurity startups in their early phases of development. By investing in promising companies, early-stage VCs help nurture innovation, accelerate product development, and enable startups to scale their operations.

Investments in Israeli Cybersecurity Startups
Israeli cybersecurity startups have attracted significant cybersecurity venture capital investments from both local and international investors. The country’s reputation for producing groundbreaking technologies and the success stories of previous cybersecurity startups have made it an attractive destination for venture capital firms and strategic investors.
Early-stage venture capital firms in Israel actively seek out cybersecurity startups with disruptive technologies and strong growth potential. These firms not only provide financial support but also leverage their extensive networks and industry knowledge to help startups navigate challenges, identify market opportunities, and connect with potential customers and partners.
Investment Trends and Areas of Focus
The investment landscape in Israeli cybersecurity is characterized by a diverse range of areas of focus. Some startups specialize in network security, while others focus on cloud security, application security, or IoT security. The growing demand for solutions in areas such as artificial intelligence (AI), machine learning (ML), and data protection has also attracted significant investments.
Q&A Section:
What are some notable succes
s stories in Israeli cybersecurity investments?
Israel has seen several notable success stories in the cybersecurity realm. Companies like Check Point Software Technologies, CyberArk, and Palo Alto Networks have emerged as global leaders in cybersecurity, with significant market presence and successful IPOs. These success stories serve as inspiration for aspiring cybersecurity startups and attract further investments in the industry.
How does the Israeli government support cybersecurity investments?
The Israeli government recognizes the strategic importance of cybersecurity and actively supports the industry. It provides various initiatives, grants, and tax incentives to promote research and development in cybersecurity. Additionally, the government collaborates with industry stakeholders to foster partnerships, encourage international collaborations, and promote Israel as a global cybersecurity hub.
Are there any unique challenges or opportunities for early-stage venture capital firms in Israel’s cybersecurity sector?
While the Israeli cybersecurity sector offers immense opportunities, it also comes with unique challenges. One challenge is the fierce competition to identify and invest in the most promising startups. With a vibrant ecosystem and a steady stream of innovative companies, early-stage venture capital firms need to carefully evaluate investment opportunities and build strong relationships with entrepreneurs to secure deals. However, the abundance of talent, strong support systems, and access to international markets make Israeli cybersecurity investments an exciting prospect for early-stage VCs.
-
3D Technology3 years ago
3D Scanner Technology for Android Phones: Unleashing New Possibilities
-
Business Solutions2 years ago
Understanding A2P Messaging and the Bulk SMS Business Landscape
-

 Business Solutions2 years ago
Business Solutions2 years agoThe Power of Smarts SMS and Single Platform Chat Messaging
-

 Automotive3 years ago
Automotive3 years agoDSRC vs. CV2X: A Comprehensive Comparison of V2X Communication Technologies
-
Tech3 years ago
On Using Generative AI to Create Future-Facing Videos
-

 Business Solutions2 years ago
Business Solutions2 years agoExploring OTP Smart Features in Smart Messaging Services
-

 Business Solutions2 years ago
Business Solutions2 years agoLive Video Broadcasting with Bonded Transmission Technology
-

 Business Solutions10 months ago
Business Solutions10 months agoThe Future of Healthcare SMS and RCS Messaging







