Business Solutions
The Basics of OTP SMS Texting
One-Time Passwords (OTP) have become indispensable in ensuring secure user verification processes, and OTP SMS remains the most popular way to deliver these codes. OTP text messages provide a simple, effective way for platforms to validate the identity of users during login, transactions, or other secure processes. This approach to security relies on a code sent via SMS, ensuring that only the intended recipient can complete the authentication process.
OTP SMS stands out because of its user-friendly approach—almost everyone carries a mobile phone capable of receiving SMS. The universality of SMS as a communication medium means that OTP texts are accessible to a broad audience without the need for additional software or special devices. This accessibility makes OTP SMS a go-to solution for companies looking to enhance user security while keeping the user experience smooth and straightforward.
One of the key benefits of OTP text messages is their limited validity. OTPs are time-sensitive, often valid for just a few minutes, which ensures that the authentication process remains secure even if the message is intercepted. This temporary nature adds an additional layer of protection, reducing the window of opportunity for cybercriminals to misuse the code.
The Anatomy of an OTP: What Makes It Tick?
To understand why OTP SMS is effective, it’s essential to know what makes an OTP functionally secure. An OTP, by design, is a unique sequence of numbers or characters that is valid only for a single use. The OTP text typically ranges between four and eight digits, making it both secure and user-friendly, as users can enter it easily without confusion.
The randomness of an OTP is one of its most critical components. OTP generation leverages algorithms that ensure the code cannot be easily predicted. Algorithms like HMAC-based OTP (HOTP) and Time-based OTP (TOTP) play a pivotal role in generating these codes, ensuring that each one is unique and valid only within a specific time window. The result is a secure and dynamic code that is virtually impossible for attackers to guess through conventional means.
Moreover, the temporal aspect of OTP SMS is equally crucial. OTP texts usually expire within 30 seconds to a few minutes, adding a dynamic component to their security. This limited window of validity means that even if an OTP is intercepted, it becomes useless after its short lifespan ends. The combination of algorithmic randomness and time restriction makes OTP SMS a formidable tool for preventing unauthorized access.
Why OTP SMS? Advantages in Authentication
OTP SMS remains a preferred choice for authentication due to its simplicity and effectiveness. Unlike traditional passwords, which are static and vulnerable to brute force attacks or leaks, OTP texts are dynamic and used only once. This one-time nature makes them significantly more secure, especially for protecting sensitive data like banking information or private communications.
A significant advantage of OTP SMS is its familiarity. Users are already accustomed to receiving SMS messages, and integrating OTPs into this channel means that there is no learning curve involved. This makes adoption easier for both individuals and businesses, minimizing friction in the authentication process.
Additionally, OTP SMS is cost-effective for businesses. Unlike other methods that require hardware tokens or specialized software, using SMS takes advantage of existing telecommunications infrastructure. With minimal upfront investment and maintenance requirements, companies can roll out OTP-based authentication to their entire user base quickly and efficiently, thereby enhancing security without incurring prohibitive costs.
The Role of OTP SMS in Multi-Factor Authentication
Multi-Factor Authentication (MFA) has become the gold standard for securing online accounts, and OTP SMS plays an essential role in this context. MFA requires users to provide two or more verification factors to prove their identity, and OTP text messages serve as an ideal second factor. Typically, the first factor is something the user knows (like a password), while the second is something they have (like an OTP sent via SMS).
By using OTP SMS as part of MFA, companies can significantly reduce the likelihood of unauthorized access. Even if an attacker manages to steal a user’s password, they still need access to the user’s mobile phone to receive the OTP, adding a critical additional barrier. This layered security approach makes it much more difficult for attackers to gain access, even if one layer of security is compromised.
Despite some concerns about the vulnerability of SMS, it remains a practical choice for many organizations because of its broad accessibility and ease of implementation. Many users are familiar with the process of receiving and entering OTPs, making it an effective and user-friendly option for enhancing account security across various platforms.
Navigating the Pitfalls: Avoiding OTP Fraud
While OTP SMS is a powerful security tool, it is not without vulnerabilities. One of the primary challenges is the potential for phishing attacks. In these attacks, cybercriminals trick users into revealing their OTP by impersonating a legitimate service. Once the OTP is handed over, the attacker can use it to gain unauthorized access to the user’s account.
To mitigate the risks of OTP fraud, user education is paramount. Users should be aware of the importance of never sharing their OTP texts with anyone, even if they appear to be from a legitimate source. Organizations can also take steps to prevent fraud by implementing anti-phishing tools and incorporating warning messages into OTP SMS, reminding users never to share their codes.
In addition, security measures like monitoring unusual activity, rate limiting, and requiring additional verification for high-risk transactions can help reduce the risk of OTP-based attacks. By recognizing and mitigating these vulnerabilities, organizations can make their OTP SMS systems more robust and resistant to fraud.
Integrating OTP SMS with Your Tech Stack
Integrating OTP SMS with an existing tech stack can significantly enhance an organization’s security framework. However, the integration process requires careful consideration to ensure compatibility and scalability. For instance, businesses must select an OTP SMS provider that offers reliable and fast message delivery across different mobile carriers.
The process often involves integrating an API that facilitates OTP SMS sending, which allows seamless communication between the business’s application and the SMS gateway. Ensuring that this integration is secure is critical. Encryption must be used to protect OTPs during transmission, and rate limits should be set to prevent abuse.
Scalability is another essential consideration. Businesses with a large user base must ensure that their OTP SMS provider can handle peak demands, especially during high-traffic events such as flash sales or product launches. Choosing a service with guaranteed uptime and low latency ensures that users receive their OTP texts promptly, minimizing friction during the authentication process.
Global Reach: OTP SMS in International Contexts
The use of OTP SMS across international borders introduces unique challenges. Varying carrier fees, regulatory restrictions, and differing network capabilities can all impact the delivery and reliability of OTP texts. For businesses with a global user base, ensuring that OTP SMS is delivered reliably and consistently to users in different regions is crucial for maintaining trust and security.
Different countries have varying regulations regarding SMS communications, particularly in terms of user consent and data privacy. Organizations must navigate these regulations to remain compliant while providing OTP services. Working with an SMS provider that has experience in international markets can help businesses overcome these challenges, ensuring consistent delivery times and minimizing the risk of messages being blocked or delayed.
Another consideration for global OTP SMS delivery is language. When sending OTP texts to users in different countries, localization becomes important. Businesses should ensure that the language of their OTP SMS messages is suitable for the recipient, improving user experience and reducing confusion.
Case in Point: Innovations Driving OTP SMS Forward
The technology behind OTP SMS is continually evolving, driven by the need for better security and user experience. One area of innovation is the integration of biometric verification with OTP SMS. By combining fingerprint or facial recognition with OTPs, businesses can offer an even higher level of security without sacrificing convenience.
Machine learning and artificial intelligence are also being utilized to enhance the OTP SMS process. AI algorithms can analyze user behavior and flag any unusual activity, which may indicate a potential security breach. By integrating AI into the OTP process, organizations can proactively address security threats before they result in a data breach.
Another innovation driving the evolution of OTP SMS is the use of encrypted SMS channels. Unlike traditional SMS, which can be vulnerable to interception, encrypted SMS ensures that OTP texts are transmitted securely, making it even harder for attackers to intercept and misuse them.
Towards a Safer Future: The Evolution of OTP SMS
As cyber threats become more sophisticated, the methods we use to protect sensitive information must also evolve. OTP SMS remains an integral part of the security landscape due to its accessibility, simplicity, and effectiveness. However, advancements in technology and the growing complexity of cyber threats mean that OTP SMS must continue to adapt.
Looking forward, we can expect OTP technologies to be more deeply integrated into multi-factor authentication systems, possibly working alongside biometric data or even behavioral analytics. Innovations like encrypted messaging, AI-driven fraud detection, and dynamic risk-based authentication will likely become standard features of OTP SMS solutions.
Business Solutions
International Air Freight for Technology Equipment: Why Speed and Compliance Are Non-Negotiable

In the world of global technology supply chains, timing is everything. A delayed server rack at a data center construction site means weeks of idle workers and escalating costs. A stalled shipment of networking equipment halts an entire enterprise rollout. For the IT industry, air freight is not simply a logistical option — it is the backbone of mission-critical global deployments.
This article explores the role of international air freight services in technology supply chains, the key challenges involved, and how specialized logistics providers deliver speed, security, and compliance when it matters most.
Why Air Freight Dominates Technology Hardware Logistics
Technology hardware has unique characteristics that make air cargo the preferred mode of transport over sea or road freight. IT equipment — from server racks and telecom base stations to cybersecurity appliances and GPU clusters — is high-value, often time-sensitive, and sometimes subject to tight project delivery windows.
The table below illustrates how air freight compares to alternative modes for technology hardware shipments:
| Factor | Air Freight | Sea/Land Freight |
| Speed | 1–5 days | 2–6 weeks |
| Cost | Higher per kg | Lower per kg |
| Suitability (IT Hardware) | Excellent | Moderate |
| Security | High (controlled handling) | Variable |
| Customs Control | Streamlined (fewer stops) | Multiple transit points |
| Ideal for | Mission-critical, time-sensitive | Bulk, cost-sensitive cargo |
For technology companies managing global deployments across multiple countries simultaneously, air freight offers the one thing no other mode can — reliable, predictable delivery times. When a data center needs to go live on a specific date, air cargo is the only option that provides that assurance.
Key Challenges in Air Freight for IT Equipment
Despite its speed advantages, international air freight for technology hardware comes with significant operational complexity. Companies that underestimate these challenges often encounter costly delays at exactly the wrong moment.
- Customs and compliance — each country imposes different import requirements for IT and telecom equipment, including certifications, permits, and encryption declarations
- Dual-use export controls — certain categories of IT hardware (encryption devices, high-performance chips, radio frequency equipment) may require export licenses
- Dangerous goods regulations — lithium batteries, capacitors, and other electronic components may be subject to IATA dangerous goods rules
- Last-mile coordination — air freight delivers to airport facilities; reaching the final site often requires dedicated import-side logistics infrastructure
- Documentation accuracy — a single error on a customs invoice can result in shipment holds lasting days or weeks in certain countries
These challenges underscore why companies shipping technology hardware internationally need specialized logistics partners — not general freight forwarders who lack industry-specific knowledge.
The Role of the Importer of Record in Air Freight
One of the most critical components of a successful international air freight shipment is having the right Importer of Record (IOR) in the destination country. The IOR assumes legal responsibility for the import, ensuring customs clearance proceeds correctly and without penalties.
For technology companies without local entities in destination markets, working with an IOR provider is essential. The IOR handles all customs documentation, pays duties and taxes, obtains any required import permits, and ensures the shipment is released and delivered to the final address.
GetWay Global provides integrated IOR services alongside its air freight operations, enabling clients to manage the full door-to-door journey through a single provider. Learn more about GetWay Global’s importer of record services for global technology hardware.
Time-Critical Air Freight: When Every Hour Counts
The technology sector frequently generates scenarios where standard air freight timelines are not fast enough. Network outages, equipment failures, and emergency infrastructure deployments can require same-day or next-flight-out logistics solutions.
Time-critical air freight services offer:
- Next-flight-out (NFO) booking for urgent cargo
- 24/7 operations support for emergency shipment management
- Pre-clearance coordination to minimize customs processing times
- Direct connections with airline priority cargo handling
- Dedicated tracking and proactive exception management
GetWay Global specializes in time-critical deliveries as part of its core service offering, particularly for IT hardware deployments where project timelines are non-negotiable. The company operates with a 24-hour SLA support framework to ensure urgent shipments are handled at the highest priority.
Regional Air Freight Considerations
Different regions present different challenges and opportunities for air freight in the technology sector:
- Latin America — high customs complexity in Brazil and Argentina requires advance planning and specialist IOR support; air cargo from Europe or North America can arrive in 1–2 days but may face 5–10 days of clearance without proper documentation
- Middle East — strong growth in UAE and Saudi Arabia’s digital infrastructure creates high demand for air cargo; Dubai acts as a major regional hub for distribution across Gulf states
- Asia — China, India, and Southeast Asia are the world’s largest manufacturers and importers of IT hardware; air freight enables rapid redistribution and emergency stock movements
- Europe — the EU single market simplifies intra-European movements, but non-EU countries require full customs compliance at each border
Sustainability in Air Freight Logistics
As technology companies face increasing pressure to reduce their carbon footprints, air freight sustainability has become a key topic. Sustainable Aviation Fuel (SAF) programs are being introduced by major carriers, and logistics providers are increasingly offering carbon offset options as part of their service portfolios.
Forward-thinking logistics companies are also optimizing consolidation strategies — combining multiple smaller shipments into single aircraft loads — to reduce emissions per unit shipped. This approach benefits technology companies managing distributed deployments across multiple customer sites.
Conclusion
International air freight for technology equipment demands more than cargo capacity — it requires regulatory knowledge, customs expertise, and a reliable network of on-the-ground partners. GetWay Global delivers exactly this combination, providing air freight services integrated with IOR capabilities, warehousing, and last-mile delivery across the world’s most complex markets.
For technology companies managing global deployments, partnerships with specialists who understand both the logistics and the compliance dimensions of international air cargo are no longer optional — they are a competitive necessity.
For further reading on logistics technology trends, visit https://alltechnews.medium.com/.
Business Solutions
Modern Breeding for Better Fresh Pepper Crops
Take a bite of a vibrant red pepper and you’re tasting the result of decades of agricultural innovation. Modern pepper breeding has transformed how farmers grow peppers and how consumers experience them, leading to a new generation of fresh pepper varieties that combine flavor, durability, and visual appeal. As global demand for fresh produce grows, breeders are working continuously to develop peppers that perform well in the field while delivering the taste and quality shoppers expect.
Across grocery stores and farmers markets worldwide, peppers are valued for their color, sweetness, and versatility. Whether used in salads, roasted dishes, or eaten raw as a snack, peppers remain one of the most popular vegetables in fresh markets. To keep pace with rising consumer expectations and environmental challenges, plant breeders are improving pepper genetics to produce crops that are both productive and resilient.
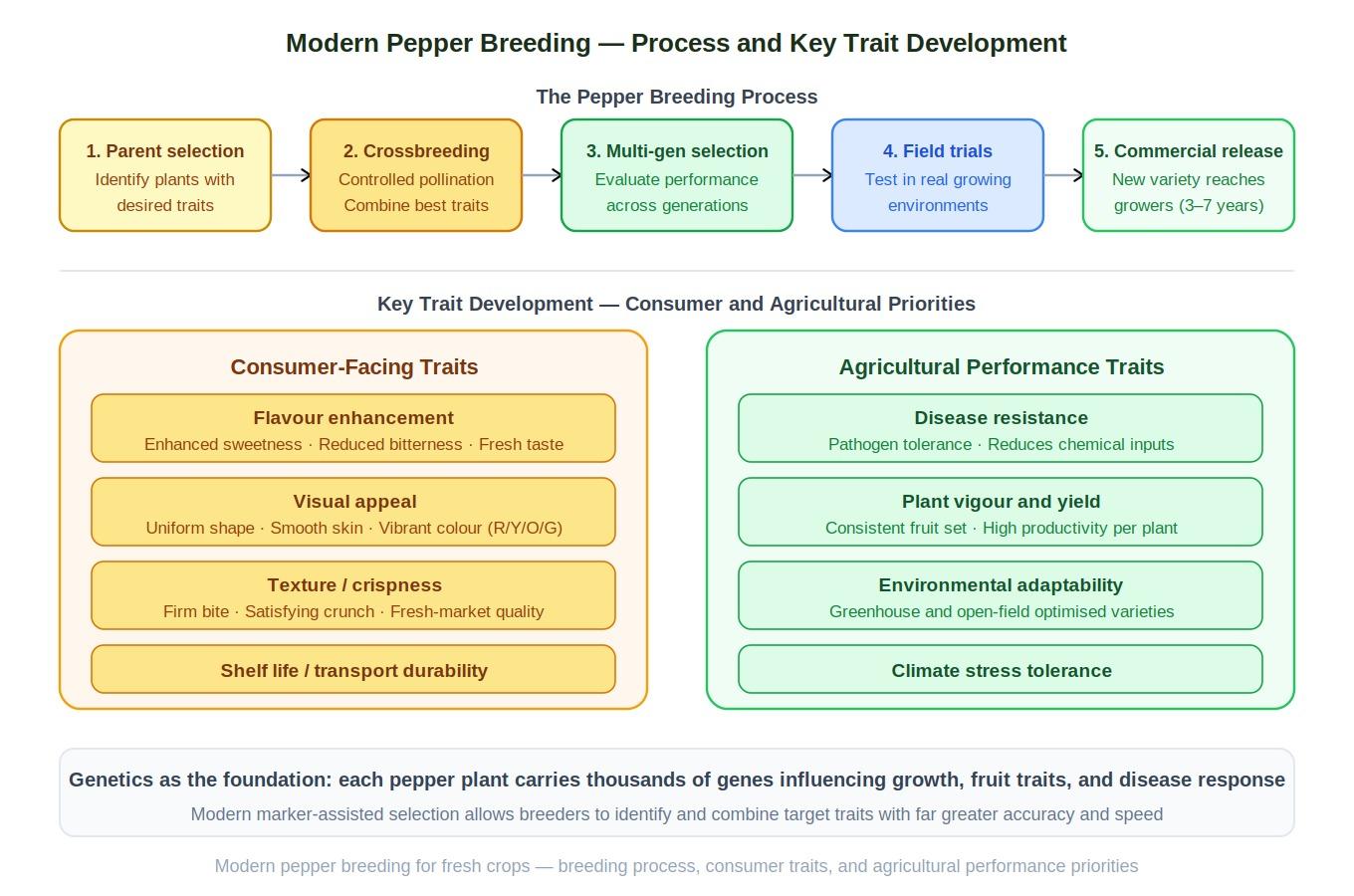
What Pepper Breeding Involves
Pepper breeding is the scientific process of developing new pepper varieties by selecting plants with desirable traits and combining them through controlled crossbreeding. The goal is to produce plants that offer improved performance for both farmers and consumers.
Breeders begin by identifying parent plants that possess valuable characteristics such as strong growth, attractive fruit shape, or exceptional flavor. These plants are crossbred to produce offspring that combine the best traits of both parents.
The resulting plants are evaluated over multiple generations. Breeders observe factors such as plant vigor, fruit quality, disease resistance, and yield. Only the strongest plants are selected for further breeding.
This process requires patience and precision, often taking several years before a new pepper variety reaches the commercial market.
Key Traits in Modern Fresh Pepper Development
Modern breeding programs focus on a range of traits that determine whether a fresh pepper variety will succeed in the marketplace. Flavor is one of the most important characteristics, as consumers increasingly expect vegetables that deliver strong taste and freshness.
Appearance also plays a significant role. Uniform shape, smooth skin, and vibrant color help peppers stand out on grocery shelves and appeal to shoppers.
Breeders also prioritize shelf life and transport durability. Peppers that remain firm and fresh during shipping help reduce waste and ensure consistent quality across supply chains.
By combining these characteristics, breeders create peppers that satisfy both agricultural performance requirements and consumer expectations.
Flavor, Color, and Consumer Appeal
Consumer preferences strongly influence breeding priorities. Over time, breeding programs have developed peppers with enhanced sweetness and reduced bitterness, making them more appealing for raw consumption.
Color diversity is another important factor. Fresh peppers appear in a wide range of shades, including green, red, yellow, orange, and even purple. These colors not only add visual appeal but also indicate different stages of ripeness and nutritional content.
Texture is equally important. Crispness is a hallmark of high-quality peppers, particularly for varieties intended to be eaten fresh.
By understanding how consumers evaluate produce, breeders can develop pepper varieties that deliver an enjoyable eating experience while maintaining agricultural reliability.
Agricultural Performance and Grower Needs
Farmers depend on crops that are reliable and efficient to grow. Pepper breeding therefore emphasizes traits that improve plant performance in real-world agricultural environments.
Disease resistance is one of the most important agricultural traits. Many pepper crops are vulnerable to plant pathogens that can reduce yield and quality. Breeding resistant varieties helps protect crops and reduces the need for chemical treatments.
Plant vigor and productivity are also critical. Strong plants with consistent fruit production allow farmers to maximize harvests while maintaining stable supply levels.
Adaptability to different growing environments is another key factor. Some pepper varieties are optimized for greenhouse cultivation, while others perform better in open-field agriculture.
Genetics and Innovation in Pepper Breeding
Genetics forms the foundation of modern crop improvement. Each pepper plant contains thousands of genes that influence its growth, fruit characteristics, and resistance to environmental stress.
By studying these genes, breeders can identify which plants carry traits that improve crop performance. Genetic diversity among pepper varieties provides a rich pool of characteristics that breeders can combine to create improved plants.
Advances in genetic research have dramatically accelerated breeding programs. Scientists can now identify genetic markers associated with valuable traits such as disease resistance or fruit sweetness.
This knowledge helps breeders focus on the most promising plant combinations, reducing the time required to develop new varieties.
Technology Accelerating Crop Development
Technological advancements have transformed the breeding process. Modern breeding programs often incorporate genomic analysis, digital imaging systems, and advanced data analytics.
Genomic tools allow researchers to analyze plant DNA and identify genes responsible for specific traits. This information helps guide breeding decisions and speeds up the development of new pepper varieties.
Digital phenotyping tools allow scientists to monitor plant growth and fruit development using automated imaging systems. These technologies provide detailed insights into how plants respond to environmental conditions.
By combining traditional breeding knowledge with advanced technology, researchers can develop improved pepper crops more efficiently than ever before.
Sustainability in Fresh Pepper Agriculture
Sustainability has become a central concern in modern agriculture. Breeding programs play a crucial role in helping farmers produce crops more efficiently while reducing environmental impact.
Improved pepper varieties may require less water, fewer fertilizers, and reduced pesticide use compared to older varieties. These traits support environmentally responsible farming practices.
Breeding also helps create plants that tolerate challenging conditions such as heat, drought, or soil variability. These improvements allow farmers to maintain productivity even as climate conditions change.
Sustainable crop development ensures that agriculture can continue providing nutritious food while protecting natural resources.
The Future of Fresh Pepper Breeding
The future of pepper breeding will likely involve even more advanced scientific tools. Artificial intelligence is beginning to assist researchers in analyzing complex genetic data and predicting plant performance.
Climate resilience will remain a key priority as breeders work to develop crops capable of thriving in increasingly unpredictable environmental conditions.
Breeding programs will also continue exploring specialty pepper varieties that appeal to evolving consumer preferences. These may include peppers with unique shapes, flavors, or enhanced nutritional content.
As agricultural science progresses, fresh peppers will continue evolving into crops that meet the needs of both farmers and consumers.
Conclusion
Fresh peppers may appear simple, but the science behind them is remarkably complex. Through careful selection, genetic research, and technological innovation, breeders have transformed peppers into highly adaptable and productive crops.
Pepper breeding continues to drive improvements in crop performance, helping farmers produce reliable harvests while delivering flavorful produce to consumers.
As agricultural challenges evolve, modern breeding programs will remain essential for developing the next generation of fresh pepper varieties that support sustainable and resilient food systems.
Business Solutions
Drone-UAV RF Communication: The Backbone of Modern Aerial Operations
Drone-UAV RF Communication is revolutionizing the way drones operate, serving as the foundation for reliable, efficient, and innovative aerial systems. From ensuring seamless connectivity to enabling advanced maneuvers, this technology plays a pivotal role in modern drone operations. Its ability to provide consistent and secure communication is what makes it indispensable for both commercial and defense applications.

Unmanned Aerial Vehicles (UAVs), commonly known as drones, have become a pivotal technology across industries such as defense, agriculture, logistics, and surveillance. At the core of a drone’s functionality is its communication system, which enables control, data transfer, and situational awareness. Radio Frequency (RF) communication plays a crucial role in ensuring that UAVs can operate effectively in a variety of environments, with high reliability and low latency. Learn more about DRONE-UAV RF COMMUNICATION.
This article delves into the significance of RF communication in Drone-UAV operations, the challenges it presents, the technologies involved, and how future advancements are shaping the communication systems for UAVs.
The Role of RF Communication in Drone-UAV Operations
RF communication is the medium through which most drones communicate with ground control stations (GCS), onboard systems, and other UAVs in a network. It enables the transmission of various types of data, including:
Control Signals: These are essential for operating the UAV, including commands for takeoff, landing, navigation, and flight adjustments.
Telemetry Data: Real-time data on the UAV’s performance, including altitude, speed, battery level, and sensor readings.
Video and Sensor Data: Drones equipped with cameras or other sensors (such as thermal, LiDAR, or multispectral) require high-bandwidth RF communication to send video feeds or sensor data back to the ground station.
Learn more about Optical Delay Line Solutions.
Payload Data: UAVs used for specific tasks like delivery or surveillance may need to transmit payload-related data, such as GPS coordinates, images, or diagnostic information.
Given the variety of data types and the need for real-time communication, a robust and reliable RF communication system is essential for the successful operation of drones in both civilian and military applications.

RF Communication Technologies for Drone-UAVs
The communication requirements of drones are diverse, necessitating different RF communication technologies and frequency bands. These technologies are designed to address challenges such as range, interference, data rate, and power consumption.
1. Frequency Bands
The RF spectrum is divided into several frequency bands, and each is used for different types of communication in UAV systems. The most commonly used frequency bands for drone communications are:
2.4 GHz: This band is one of the most popular for consumer-grade drones. It offers a good balance of range and data transfer speed, although it is prone to interference from other wireless devices (such as Wi-Fi routers and Bluetooth devices).
5.8 GHz: This band is often used for high-definition video transmission in drones, as it offers higher data rates than 2.4 GHz, but with a slightly shorter range. It’s less crowded than 2.4 GHz and typically experiences less interference.
Sub-1 GHz (e.g., 900 MHz): This frequency is used for long-range communications, as lower frequencies tend to travel farther and penetrate obstacles more effectively. It’s ideal for military drones or those used in remote areas.
L, S, and C Bands: These bands are used in military and commercial UAVs for long-range communication, often for surveillance, reconnaissance, and tactical operations. These frequencies have lower susceptibility to interference and are better suited for higher-power transmissions.
2. Modulation Techniques
The RF communication system in drones uses different modulation techniques to efficiently transmit data. Modulation refers to the method of encoding information onto a carrier wave for transmission. Some common modulation techniques used in UAV RF communication include:
Frequency Modulation (FM): Often used in control signals, FM is simple and efficient, providing clear communication with minimal interference.
Amplitude Modulation (AM): Used for video and lower-bandwidth applications, AM transmits a signal whose amplitude is varied to carry the information.
Phase Shift Keying (PSK) and Quadrature Amplitude Modulation (QAM): These more advanced techniques allow for high data transfer rates, making them ideal for transmitting high-definition video or large sensor datasets.
3. Signal Encoding and Error Correction
To ensure that RF communication remains stable and reliable, especially in noisy or crowded environments, drones use advanced signal encoding and error correction methods. These techniques help to mitigate the impact of signal interference, fading, and packet loss. Common methods include:
Forward Error Correction (FEC): This involves adding redundant data to the so that errors can be detected and corrected at the receiver end.
Diversity Reception: Drones may employ multiple antennas or receivers, allowing them to receive signals from different directions and improve the overall reliability of communication.
Spread Spectrum Techniques: Methods like Frequency Hopping Spread Spectrum (FHSS) or Direct Sequence Spread Spectrum (DSSS) spread the signal over a wider bandwidth, making it more resistant to jamming and interference.
4. Long-Range Communication
For long-range missions, RF communication technology needs to go beyond traditional line-of-sight communication. To achieve this, drones can leverage various technologies:
Satellite Communication (SATCOM): When beyond-visual-line-of-sight (BVLOS) operations are required, drones can use satellite links (via L, S, or Ku-band frequencies) to maintain constant communication with the ground station.
Cellular Networks: 4G LTE and 5G networks are increasingly being used for drone communication, especially in urban environments. 5G, in particular, offers ultra-low latency, high-speed data transfer, and extensive coverage.
Mesh Networking: Some UAVs can form mesh networks where each drone communicates with others in the fleet, extending the range of the communication system and providing redundancy.
Challenges in Drone-UAV RF Communication
While RF communication is essential for UAVs, it presents several challenges that need to be addressed to ensure the reliable and secure operation of drones.
1. Interference and Jamming
One of the biggest threats to RF communication in drones is interference from other electronic systems or intentional jamming. Drones, especially in crowded or military environments, must be capable of avoiding interference from various sources, such as:
Other drones operating on the same frequencies.
Wireless communication systems like Wi-Fi or Bluetooth.
Intentional jamming by adversaries in conflict zones or hostile environments.
To mitigate these issues, drones use frequency hopping, spread spectrum techniques, and advanced error-correction algorithms to make communication more resilient.
2. Limited Range and Power Constraints
The effective range of RF communication in drones is limited by factors such as transmitter power, antenna design, and frequency band characteristics. While UAVs with longer ranges can use lower frequencies like 900 MHz or satellite links, they are often limited by battery life and payload capacity.
The trade-off between range and power consumption is an ongoing challenge. Drones must find a balance between maintaining communication and extending their operational flight times.
3. Security Risks
The RF communication channel is vulnerable to security threats, such as signal interception, spoofing, and hacking. Unauthorized access to the communication link could compromise the integrity of the UAV’s operations or allow malicious actors to take control of the drone.
To secure drone communications, encryption methods like AES (Advanced Encryption Standard) and TLS (Transport Layer Security) are employed, ensuring that only authorized parties can decrypt and interpret the transmitted data.
4. Latency and Data Throughput
For applications that require real-time control and feedback, such as autonomous drones or those used in first-responder scenarios, low-latency communication is crucial. High latency could delay mission-critical decisions, especially in dynamic environments like search and rescue operations or military engagements. Additionally, high-data-throughput applications like video streaming require RF systems with robust bandwidth management.
Future Trends in Drone-UAV RF Communication
As UAV technology continues to advance, so will the communication systems that power them. Key trends in the future of drone RF communication include:
5G and Beyond: The rollout of 5G networks is expected to revolutionize drone communications with ultra-low latency, high bandwidth, and greater network density. This will enable more drones to operate simultaneously in urban environments, enhance remote operation, and facilitate advanced applications such as drone swarming and real-time video streaming.
Artificial Intelligence (AI) for Dynamic Communication: AI-powered algorithms can optimize communication links based on environmental conditions, such as avoiding interference, adjusting frequencies, and ensuring maximum data throughput. AI will also play a role in improving autonomous decision-making for UAVs in communication-heavy operations.
Integration with IoT: Drones are increasingly integrated into the Internet of Things (IoT) ecosystem. As a result, drones will not only communicate with ground control but also with other devices and systems in real-time. This opens new possibilities for industrial applications like smart farming, precision delivery, and environmental monitoring.
RF communication is at the heart of every drone’s operation, whether for military, industrial, or commercial use. As UAV technology continues to evolve, so too must the communication systems that support them. RF communication technologies are enabling drones to perform increasingly complex tasks, from surveillance and reconnaissance to logistics and environmental monitoring.
Despite the challenges posed by interference, range limitations, and security risks, advances in RF technology, coupled with innovations like 5G and AI, promise to take UAV communication systems to new heights—fostering more reliable, secure, and efficient operations across a range of industries.
-

 Business Solutions2 years ago
Business Solutions2 years agoLive Video Broadcasting with Bonded Transmission Technology
-

 Business Solutions11 months ago
Business Solutions11 months agoThe Future of Healthcare SMS and RCS Messaging
-

 Business Solutions2 years ago
Business Solutions2 years ago2-Way Texting Solutions from Company Message Services
-

 Business Solutions2 years ago
Business Solutions2 years agoCommunication with Analog to Fiber Converters & RF Link Budgets
-

 DSRC Communication1 year ago
DSRC Communication1 year agoThe Crossroads of Connectivity: DSRC vs. C-V2X Technologies in Automotive Communication
-
Electronics2 years ago
AI Modules and Smart Home Chips: Future of Home Automation
-
 Tech3 years ago
Tech3 years agoThe Symphony of Connectivity: Understanding Ethernet Devices
-

 Business Solutions2 years ago
Business Solutions2 years agoWholesale SMS Platforms with OTP Services







